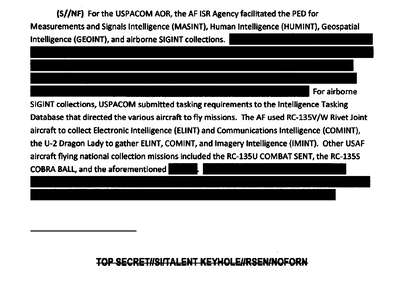
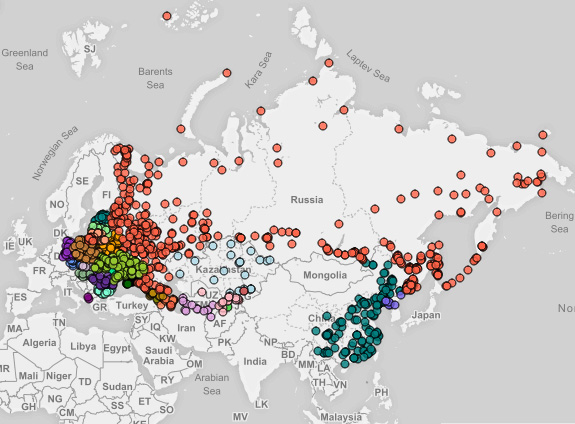
The Canadian government is “really worried” about cyber attacks that have targeted critical infrastructure and has helped companies improve their defenses without disclosing hacks to the public, a senior intelligence official said on Monday.
The comment by Scott Jones, an assistant deputy minister at Canada’s Communications Security Establishment intelligence agency, follows a warning on Friday from the United States that sophisticated hackers are targeting U.S. infrastructure, including nuclear, energy, aviation, water and manufacturing industries.
Malware Campaign Targets Security Researchers with Bogus Cyber Conference Document
Hackers Group 74 (a.k.a. Tsar Team, Sofacy, APT28, or Fancy Bear)—a Russian hacking collective with links to the Kremlin—are using fake messages from the Cyber Conflict US conference to infect cybersecurity experts with malware, according to a new report from Cisco Talos.
The attack is particularly effective because its decoy document is from a real conference: The Cyber Conflict US conference organized by the NATO Cooperative Cyber Defence Centre of Excellence, which is taking place on November 7-8 in Washington, DC.
Cybersecurity workers received an email with an attached two-page Word document labeled "Conference_on_Cyber_Conflict.doc." The fake flyer contains a malicious Visual Basic for Applications (VBA) macro. Previous campaigns from Group 74 included Office exploits or zero-day attacks, Cisco Talos researchers noted in their report.
CyCon U.S. is a collaboration between the Army Cyber Institute at the U.S. Military Academy and the NATO Cooperative Cyber Defense Centre of Excellence, based in Tallinn, Estonia, where the complementary CyCon Conference is held every spring.
Irony Alert: The theme of this year's CyCon U.S. is "The Future of Cyber Conflict."
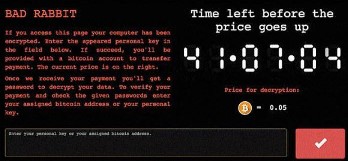
Fear the Reaper: Calm Before the IoT Security Storm? - New botnet malware could disrupt Internet services
It’s been just over a year since the world witnessed some of the world’s top online Web sites being taken down for much of the day by “Mirai,” a zombie malware strain that enslaved “Internet of Things” (IoT) devices such as wireless routers, security cameras and digital video recorders for use in large-scale online attacks.
Now, experts are sounding the alarm about the emergence of what appears to be a far more powerful strain of IoT attack malware — variously named “Reaper” and “IoTroop” — that spreads via security holes in IoT software and hardware. And there are indications that over a million organizations may be affected already."We are likely enjoying a period of false calm before another humbling IoT attack wave breaks."
Reaper's masters and purpose are unknown, though the most obvious use for it would be a distributed denial of service attack, a la Mirai, Horowitz said.
"Such an attack could either be for the sake of general chaos, or more targeted at a specific country," she said.










 ...
...























/cdn.vox-cdn.com/uploads/chorus_image/image/57380889/robutt.0.gif)
































.gif)