drone [drohn]: from a West Germanic verb meaning ‘resound, boom’; related to Dutch dreunen ‘to drone,’ German dröhnen ‘to roar,’ and Swedish dröna ‘to drowse.’
A whirling buzz overhead, constant and pervasive. Before the drone, the sky was silent, now silence is redefined as drone. The sky is white noise.
Bugsplats and Jackpots. US Military Drone Operators Enjoy Gamers’ Delight
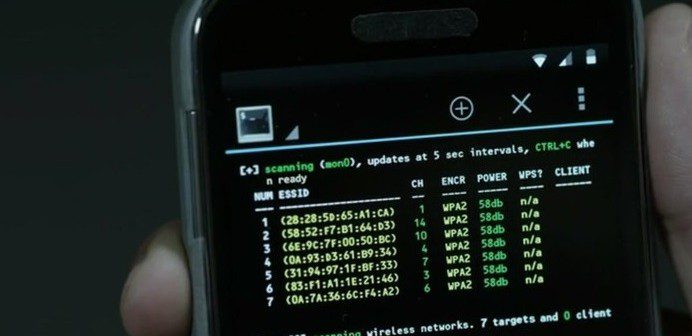
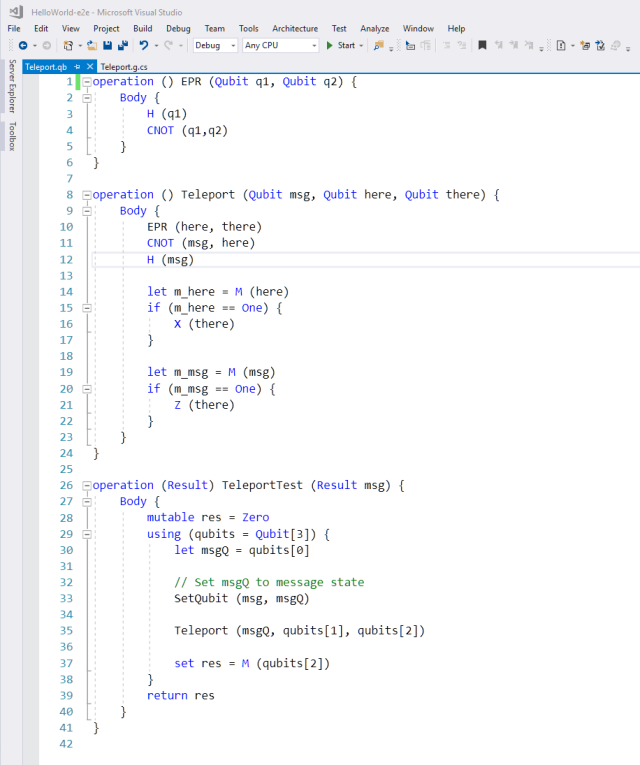
What is unique and disturbing about the US’ contemporary drone wars is the manner in which gaming technologies have now become effectively enmeshed within the operational field of war.
Remarking on the crossover between gaming technologies and drone operations, Predator sensor operator, Staff Sgt. Nicolette Sebastian, explains:... “drone operation is a lot like Play Station … ‘Oh, it’s a gamer’s delight.’”
The drone console here becomes interchangeable with that of a computer game, as drone pilots upload their own civilian computer games into the same system. A continuum between civilian gaming technologies and lethal military systems is thereby established that signals the increasing gamification of war.
The US military, in fact, has modelled the design of drone flight controls on key aspects of computer game technologies : “The flight controls for drones over the years have come to resemble video-game controllers, which the military has done to make them more intuitive for a generation of young soldiers raised on games like Gears of War and Killzone.”
https://media.giphy.com/media/10kbAgXRBGAKzK/giphy.gif
https://hackadaycom.files.wordpress.com ... .gif?w=800
https://i.makeagif.com/media/2-16-2015/KLjU76.gif
Collateral Damage
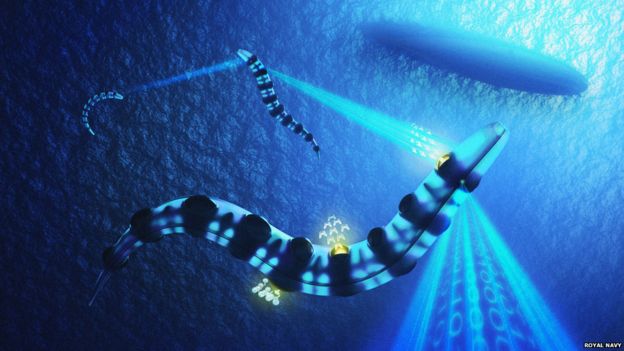
US Navy Will Use Xbox Controllers to Steer Submarine Periscopes
The Pentagon might have to buy Xbox controllers en masse in the future if the military ends up using them to control its laser weapons and other equipment. In fact, the US Navy will begin stocking its modernized Virginia-class submarines with them, starting with the USS Colorado that's expected to be commissioned in November. Sailors aboard the high-tech submarine will use the Xbox controller to maneuver its periscope. See, unlike periscopes in movies, wherein a single person has to peer through an eyepiece, the high-tech version of the instrument uses high-resolution cameras and displays images on big screens.
It's been replaced with two photonics masts that rotate 360 degrees. They feature high-resolution cameras whose images are displayed on large monitors that everyone in the control room can see. There's no barrel to peer through anymore; everything is controlled with a helicopter-style stick.
Sounds cool, right? Problem was, the joystick and the control panel Lockheed Martin developed to steer it cost around $38,000. Plus, the joystick was heavy and clunky, and it takes hours to train a sailor to use it. When the military contractor tested the Xbox controller as a replacement, sailors were able to figure out controls on their own within a few minutes. Considering each controller will only set the Navy back $30, scrapping the pricey specialized joystick and panel was a no-brainer.
The idea to switch to gaming peripherals comes from Lockheed-Martin’s classified research lab in Manassas, Virginia, which is lovingly referred to as “Area 51.”
Russia's Unmanned Aircraft Are Getting Lethal New Munitions
Russian engineers have designed munitions specifically for the nation’s unmanned aerial vehicle (UAV) fleets, according to RIA-Novosti news agency. The weapon’s combat weight is up to fifty kilograms (110lb). In effect, Russians have built precision-guided weapons for their UAVs. According to RIA, the developers are designating these weapons as “air-borne delivery vehicles.” This family of missiles is weighing fifteen, twenty-five, fifty and one hundred kilograms, and is intended for warhead delivery of up to fifty kilograms for a range of twelve to twenty kilometers (seven to thirteen miles) in the “glide mode,” and up to one hundred kilometers (sixty-two miles) when powered by the engine.
Although Russian military may have used such simple payload delivery in combat zones like Syria, the recent RIA announcement about guided munitions will greatly extend Russia's reach in its military area of operations. However, there is a major caveat—such weapons must be carried on larger and heavier UAVs that Russia currently does not have in its arsenal.
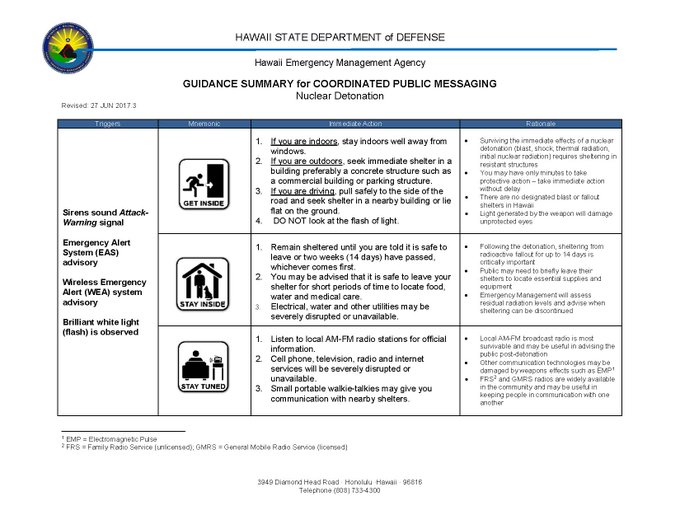
The New Dogs of War: The Future of Weaponized Artificial Intelligence
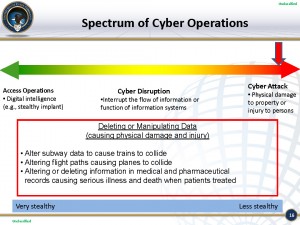
Destabilization is well-known as a tactic for weakening traditional organizations. From economic destabilization to terror attacks, adversaries try to instigate or capitalize on the destabilization (of troops, communication, sustenance, etc.) of an enemy to gain strategic advantage. Each destabilization
can ultimately threaten the national security of the impacted country.
Several of the threats modeled in this report ultimately brought about a destabilization of trust for the United States including a decrease of trust in the economy, trust of the accuracy of technology, or trust that a citizen has in their government and societal structures. Destabilizations like these may be brought about by job loss, economic downturn, and failure of medical infrastructures to adequately give care.
Current conversations regarding the potentially destabilizing effects of rampant AI represent a bleak view of the future. A massive terror attack is not the only way to undermine the normal functioning of American society. A threat actor could target the destabilization of trust, nudging, swaying and ultimately
convincing citizens that we are socially or biologically doomed and that the government will be of no help.
Destabilization events have already begun to occur on smaller scales. Equifax?
UK Scientists Edit DNA of Human Embryos
Roboticists Just Passed a 'Final Barrier' for Lifelike Robots
A new synthetic muscle developed by researchers at Columbia University in New York looks to be the next step toward smooth-moving machines becoming part of our reality. In a study published in Nature Communications, research group leader Hod Lipson, Ph.D., and his team explain that synthetic muscle can change in elasticity and volume because the muscle made of a silicone rubber matrix contains ethanol-carrying microbubbles. The results are robotic muscles like this:
Engineers from the school’s Creative Machines Lab announced Tuesday that they have developed a 3D printable synthetic soft muscle that’s three times stronger than actual human muscle. This material is the first synthetic muscle able to withstand both high actuation stress and high strain, a breakthrough that means the team has “overcome one of the final barriers to making lifelike robots.”
This synthetic muscle can push, pull, bend, twist, and lift weight, which makes it the closest match to natural muscle that’s ever been created.
This bubble-filled mixture can be 3D-printed into the desired shape, then electrically actuated — that is, brought to life — by inserting a thin, resistive wire. With a strain density that’s 15 times larger than natural muscle, robots equipped with this muscle could hypothetically lift 1,000 times their own weight.
Robot Security Guard Maker Knightscope Shows Off New Multi-terrain Model
Knightscope hires out its bots to companies for around $7 an hour (although the price for the new K7 is not yet known). That’s half the cost of a human security guard, but Knightscope’s bots offer a pretty limited service by comparison.
They can patrol, detect intruders, and scan license plates, but can’t apprehend someone, and nor can customers program the bots themselves. They’re more like advanced, mobile CCTV cameras, with their technologically-impressive presence acting as an extra deterrent. Just a shame none of the new robots float.
Fired: Prudential Center Robot is Escorted Out
Thank You for your service!
NXT Robotics Unveils Scorpion 2
San Diego-based NXT Robotics has introduced Scorpion 2, a rugged all-terrain and all-weather outdoor security robot designed to provide organizations with round-the-clock physical security monitoring and reporting capabilities. The first version of Scorpion was rolled out earlier this year at West 2017 in San Diego.
Scorpion 2, according to CTO/Founder Jeff Debrosse, is an autonomous security patrol that lowers costs while maximizing physical security surveillance capabilities. Scorpion 2 is designed for places such as military facilities, power plants, borders, parking structures, farms and ranches, and seaports.
Robots 'could take 4m UK private sector jobs within 10 years'















































/cdn.vox-cdn.com/uploads/chorus_asset/file/9381077/IMG_8767.JPG)