The machine, called AI-MATHS, scored 105 out of 150 in 22 minutes. Students have two hours to complete the test, the official Xinhua news agency reported. It then spent 10 minutes on another version and scored 100.
Beijing liberal art students who took the maths exam last year scored an average of 109.
"I hope next year the machine can improve its performance on logical reasoning and computer algorithms and score over 130," Lin Hui, the company's CEO, was quoted as saying by Xinhua.
"This is not a make-or-break test for a robot. The aim is to train artificial intelligence to learn the way humans reason and deal with numbers," Lin said.
The machine took only one of the four subjects in the crucially important entrance examination, the other three being Chinese, a foreign language and one comprehensive test in either liberal arts or science.
Fully Automated Combat Robots Pt. 2
Re: Fully Automated Combat Robots Pt. 2
AI Gets Average Grade In Chinese University Entrance Exam
“There are three classes of people: those who see. Those who see when they are shown. Those who do not see.” ― Leonardo da Vinci
Insensible before the wave so soon released by callous fate. Affected most, they understand the least, and understanding, when it comes, invariably arrives too late.
Insensible before the wave so soon released by callous fate. Affected most, they understand the least, and understanding, when it comes, invariably arrives too late.
-

vox_mundi - Intermediate Crude

- Posts: 3939
- Joined: Wed 27 Sep 2006, 03:00:00
Re: Fully Automated Combat Robots Pt. 2
Self-flying plane: Boeing To Test Pilotless Jetliners In 2018
Boeing reveals plans for fleet of giant robotic underwater military drones
Japan's SoftBank Acquires Google's Boston Dynamics and Schaft
The Robot Future Won't Need a Lot More Electricity
DeepMind takes a shot at teaching AI to reason with relational networks
Autonomous Machines Edge Towards Greater Independence
Aerospace giant Boeing has announced that it will test some of its jetliners next year without pilots leading to flying its passenger aircraft autonomously some day.
While self-driving technology for cars is relatively new, autopilot on aeroplanes have existed for over a decade. However, autopilot mode is mostly used when the aircraft is in the skies that too monitored by the pilots. The crucial task of take-off and landing are still a pilot's core responsibility even though some onboard flight computers do posses the technology to take off and land on its own."A self-flying plane would need to be able land safely as Captain Chesley Sullenberger did in the 'Miracle on the Hudson.' If it can't, then we can't go there," says Sinnett.
BAE Systems, the British defence company, has been testing robotic planes since last year and has successfully logged trials with its autonomous technology that has taken over the controls 15,000ft high in the sky.
Boeing reveals plans for fleet of giant robotic underwater military drones
Boeing's giant underwater military drone programme has been given a boost after it announced a partnership with the US's largest shipbuilding company Huntington Ingalls, which will see the development of a fleet of futuristic unmanned vehicles.
As part of the Navy's Advanced Undersea Prototyping programme, Boeing is already working on the Echo Voyager – a giant sub-like drone with the ability to fire missiles or stay underwater for months at a time to collect data. Huntington Ingalls is expected to join the project of the 51-foot drone and will continue to collaborate on new undersea drones and vehicles.
The new Echo Voyager, Boeing's secret Phantom Works division has brought us yet another step closer to robotic domination of land, sea, and air. 51 feet long, weighing 50 tons, capable of diving to 11,000 feet and ranging autonomously for up to six months at a time, it's Boeing's first unmanned undersea vehicle (UUV) that doesn't require a support ship.
Japan's SoftBank Acquires Google's Boston Dynamics and Schaft
We knew that Masayoshi Son, founder and CEO of telecom giant SoftBank, loved robots. Now the Japanese billionaire is about to significantly expand his collection.
Minutes ago, SoftBank announced that it will be acquiring Boston Dynamics and Schaft from Google parent Alphabet for an undisclosed sum, in order to “collaborate in advancing the development of smart robotics technologies.”
Boston Dynamics and Schaft were two of the nine robot companies that Google bought in 2013 to form the core of its robotics division, headed by Android founder Andy Rubin.
No more Spot or Atlas to dress up and kick around anymore
The Robot Future Won't Need a Lot More Electricity
In automated factories, less power is needed for lights and air conditioning.
As an example: Germany has a heavily industrial economy, and its producers are automating as much as possible. Siemens, for one, has boosted production at one factory ninefold in three decades without appreciably increasing its workforce. Yet, as a whole, Germany uses 5 percent less electricity than it did 10 years ago.
Where robots require significant electrical load, they create an economic incentive to conserve electricity elsewhere -- in lighting and heating, for example, which serve humans more than machines. The potential for near-total automation -- and with it the “lights-out factory” devoid of human labor -- would greatly reduce or eliminate the systems designed to keep people comfortable.
In Google’s data centers, the temperature is 80 degrees Fahrenheit (27 degrees Celsius) in the “cold aisle” sections where people work, and 120 degrees elsewhere. And the ambient noise is so loud, humans can't enter without ear protection. Continue the process of automation, and more energy-consuming systems disappear. No people means no refrigeration, no cooking, no TVs in the break room.
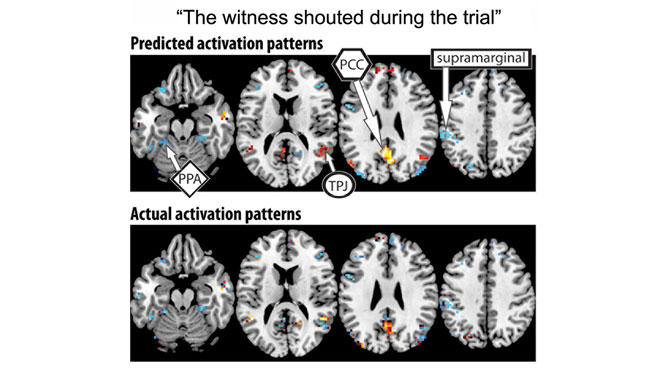
DeepMind takes a shot at teaching AI to reason with relational networks
Reasoning Is One Part of the Puzzle to Artificial General Intelligence (AGI)
Analysis The ability to think logically and to reason is key to intelligence. When this can be replicated in machines, it will no doubt make AI smarter.
But it’s a difficult problem, and current methods used in deep learning aren’t advanced enough. Deep learning is good for processing information, but it can struggle with reasoning.
Enter a different player to the game: relational networks, or RNs.
RNs are described as “plug-and-play” modules. They are designed in a way where the architecture allows the network to focus on the relationship between pairs of objects. It can be thought of as being similar to a graph network, where the nodes are objects and the edges connecting the nodes are the relationships between them.
In the CLEVR dataset, the network is presented with several objects with different shapes, sizes and textures, and is asked a series of questions that test its visual reasoning capabilities:
The word embedding of the question allows the RN to focus on the relevant pairs of objects and calculate the relation to spit out an answer. It’s clever trickery that allows a single function to work out each relation. Researchers do not have to code a function that looks at shape, and another one for size. It means RNs can be more efficient with data.
“State-of-the-art results on CLEVR using standard visual question answering architectures are 68.5 per cent, compared to 92.5 per cent for humans. But using our RN-augmented network, we were able to show super-human performance of 95.5 per cent,”DeepMind said in a blog post.
The RN has also shown promising signs that it can reason with language. The bAbI dataset, popularized by Facebook’s AI research team, is composed of 20 question-answering tasks that evaluate deduction, induction and counting skills.
First a few facts are given, such as, “Sandra picked up the football” and “Sandra went to the office,” before a question like “Where is the football?” is asked. The RN managed to pass 18 out of 20 tasks, beating previous attempts that used memory networks used by Facebook and DeepMind’s differentiable neural computer.
Autonomous Machines Edge Towards Greater Independence
In a study published in EPJ B, Agustín Bilen and Pablo Kaluza from Universidad Nacional de Cuyo, Mendoza, Argentina show that smart systems can evolve autonomously to perform a specific and well-defined task over time. Applications range from nanotechnology to biological systems, such as biological signal transduction networks, genetic regulatory networks with adaptive responses, or genetic networks in which the expression level of certain genes in a network oscillates from one state to another.
These autonomous systems do not need an external tutor. Nor do they report to a central unit designed to modify what the system must learn depending on their performance. To increase their autonomy, the authors have built in delayed dynamics and a feedback loop with the system's performance. The delayed dynamics provide information on the history of the system, thus presenting the past relationships between its structure and performance. In turn, the feedback loop offers information on the system's actual performance in terms of how close it is to the desired task.
Agustín M. Bilen et al, Autonomous learning by simple dynamical systems with a discrete-time formulation, The European Physical Journal B (2017).
“There are three classes of people: those who see. Those who see when they are shown. Those who do not see.” ― Leonardo da Vinci
Insensible before the wave so soon released by callous fate. Affected most, they understand the least, and understanding, when it comes, invariably arrives too late.
Insensible before the wave so soon released by callous fate. Affected most, they understand the least, and understanding, when it comes, invariably arrives too late.
-

vox_mundi - Intermediate Crude

- Posts: 3939
- Joined: Wed 27 Sep 2006, 03:00:00
Re: Fully Automated Combat Robots Pt. 2
DoD Considers 'Performance Enhancing Drugs' for Special Ops 'Super Soldiers'
USSOCOM Wants Performance-enhancing products for its Military Working Dogs
DARPA: Engineering Humans for War
CRISPR gene editing can cause hundreds of unintended mutations
US Special Operations Command is weighing the use of nutritional supplements or performance-enhancing drugs to push the abilities and endurance of its forces beyond current human limits, according to a report from Defense News.
While special-operations forces already have access to specialized resources, like dietitians and physical therapists, SOCOM is looking to increase their ability to tolerate pain, recover from injuries, and remain physically able in challenging environments.
"If there are ... different ways of training, different ways of acquiring performance that are non-material, that's preferred but in a lot of cases we've exhausted those areas," Ben Chitty, the senior project manager for biomedical, human performance, and canine portfolios at US SOCOM's Science and Technology office, told Defense News.One goal of the research to develop what Defense News referred to as "super soldiers" would be to expand troops' ability to operate in places not well suited for humans — high altitudes or underwater in particular.
Any proposal to deploy pharmaceutical substances among special-operations troops is likely to draw scrutiny, especially in light of recent revelations about what Capt. Jamie Sands, the commander of 900 Navy SEALs on the East Coast, called a "staggering" number of drug cases among Navy Special Operations units.
"We've been operating at such a high [operational] tempo for the last decade plus, and with budgets going down, what we've had to do is essentially ... eat our young, so to speak," Theresa Whelan, principal deputy assistant secretary of defense for special operations, said during a House Armed Services Committee session this month.
"We've mortgaged the future in order to facilitate current operations that has impacted readiness and it's also impacted development of force for the future," she said. "And as the threats grow, this is only going to get worse."
USSOCOM Wants Performance-enhancing products for its Military Working Dogs
U.S. Special Operations Command is looking for more effective ways to unleash the hounds of war.
The command headquartered at MacDill Air Force Base is asking small business to develop nutrients or pharmaceutical products that will enhance the performance of its own working dogs. At the same time, SOCom is seeking ways to inhibit the work of dogs used by the enemy.
SOCom relies on dogs for jobs like detecting explosives and enemy personnel and works to keep enemy dogs from exposing its secrets.
So the command submitted a request last month through the Pentagon's Small Business Innovation Research portal for companies interested in developing the necessary products.
SOCOM is seeking products that optimize hearing, vision and scent, improve recovery time when wounded, and increase survivability.The goal of this technology pursuit is to develop innovative pharmaceutical compounds that will optimize the performance, improve recovery time and increase the survivability of MPCs by:
• Increasing endurance
• Improving ability to regulate body temperature
• Improving hydration
• Improving acclimatization to acute extremes in temperature, altitude, and/or time zone changes
• Increase the speed of recovery from strenuous work
• Improving hearing
• Improving vision
• Improving scent
• Decreasing adverse effects and increase surviving trauma due to loss of a high volume of blood loss
https://sbir.defensebusiness.org/topics?topicId=28758
https://sbir.defensebusiness.org/topics?topicId=28757
The nutraceutical and/or pharmaceuticals will have potential commercial applications outside of USSOCOM
Cry Havoc and Let Slip the Dogs of War
DARPA: Engineering Humans for War
... It was the collapse of the Soviet Union that accelerated many of DARPA’s most radical super-soldier science programs. The revelation that the Soviets had developed an extensive biological-weapons program caused DARPA to bring biologists into its ranks, and with the life sciences at the fore, DARPA began to look inside the human body, toward a scientific capability that could transform soldiers from the inside out.
The turn of the century “was a radical time to be at DARPA,” Goldblatt said. He believed that defense sciences could demonstrate that “the next frontier was inside of our own selves,” and he became a pioneer in military-based transhumanism—the notion that man can alter the human condition fundamentally by augmenting the body with machines and other means. At the time, the threat from biological warfare was in his words “growing far faster than the solutions were coming in. … [President] Clinton gave lots of money to the countermeasures program for unconventional pathogens,” with the result that DARPA had plenty of funding for biology programs. Goldblatt saw the creation of the super-soldier as imperative to 21st-century warfare.
Goldblatt ran the DSO until 2004, and when he spoke to me last year, he could only describe unclassified programs. More than 10 years after his departure, the status of the “super-soldier” pursuits he helped launch is murky; DARPA’s highest-risk, highest-payoff programs remain secret until they are unveiled on the battlefield. Still, given the progress of the exoskeleton, these or similar programs could be closer to reality than anyone realizes.“Soldiers having no physical, physiological, or cognitive limitation will be key to survival and operational dominance in the future”
“Soldiers having no physical, physiological, or cognitive limitation will be key to survival and operational dominance in the future,” Goldblatt told his program managers a few weeks after his arrival. One program in the DSO, called Persistence in Combat, addressed three areas that slowed soldiers down on the battlefield: pain, wounds, and excessive bleeding.
Goldblatt hired a biotechnology firm to develop a pain vaccine. If a soldier got shot, Goldblatt explained, the vaccine would “reduce the pain triggered by inflammation and swelling,” the desired result being “10 to 30 seconds of agony then no pain for 30 days.” Such a vaccine would allow the warfighter to keep fighting so long as bleeding could be stopped. To develop new ways to try to stop bleeding, Goldblatt initiated another program that involved injecting millions of microscopic magnets into a person, which could later be brought together into a single area to stop bleeding with the wave of a wand.
Sleep, too, was a focus of intense research at DSO. In the Continually Assisted Performance program, scientists worked on ways to create a “24/7 soldier,” one who required little or no sleep for up to seven days. If this could be achieved, an enemy’s need for sleep would put him at an extreme disadvantage. Goldblatt’s program managers hired marine biologists studying certain sea animals to look for clues. Whales and dolphins don’t sleep; as mammals, they would drown if they did. Unlike humans, they are somehow able to control the lobes of their left and right brains so that while one lobe sleeps, the opposite lobe stays awake, allowing the animal to swim. While some DARPA scientists ruminated over the question of how humans might one day control the lobes of their own brains, other scientists experimented with drugs like Modafinil, a powerful medication used to counter sleep apnea and narcolepsy, to keep warfighters awake.
Other programs explored other questions. What if soldiers could have 10 times the muscle endurance of enemy soldiers? What if they could leap seven feet or do 300 pull-ups a day? Under the DSO banner, in a program called the Brain-Machine Interface, DARPA scientists studied how brain implants could enhance cognitive ability. … Imagine a time when the human brain has its own wireless modem so that instead of acting on thoughts, warfighters have thoughts that act,” Eisenstadt suggested. But a 2008 report by defense scientists raised some warnings. “An adversary might use” brain technology “in military applications. … An extreme example would be remote guidance or control of a human being.”
CRISPR gene editing can cause hundreds of unintended mutations
As CRISPR-Cas9 starts to move into clinical trials, a new study published in Nature Methods has found that the gene-editing technology can introduce hundreds of unintended mutations into the genome.
The first clinical trial to deploy CRISPR is now underway in China, and a U.S. trial is slated to start next year. But even though CRISPR can precisely target specific stretches of DNA, it sometimes hits other parts of the genome. Most studies that search for these off-target mutations use computer algorithms to identify areas most likely to be affected and then examine those areas for deletions and insertions.
"These predictive algorithms seem to do a good job when CRISPR is performed in cells or tissues in a dish, but whole genome sequencing has not been employed to look for all off-target effects in living animals," says co-author Alexander Bassuk, MD, PhD, professor of pediatrics at the University of Iowa.
In the new study, the researchers sequenced the entire genome of mice that had undergone CRISPR gene editing in the team's previous study and looked for all mutations, including those that only altered a single nucleotide.
The researchers determined that CRISPR had successfully corrected a gene that causes blindness, but Kellie Schaefer, a PhD student in the lab of Vinit Mahajan, MD, PhD, associate professor of ophthalmology at Stanford University, and co-author of the study, found that the genomes of two independent gene therapy recipients had sustained more than 1,500 single-nucleotide mutations and more than 100 larger deletions and insertions. None of these DNA mutations were predicted by computer algorithms that are widely used by researchers to look for off-target effects.
"Researchers who aren't using whole genome sequencing to find off-target effects may be missing potentially important mutations," Dr. Tsang says. "Even a single nucleotide change can have a huge impact."
“There are three classes of people: those who see. Those who see when they are shown. Those who do not see.” ― Leonardo da Vinci
Insensible before the wave so soon released by callous fate. Affected most, they understand the least, and understanding, when it comes, invariably arrives too late.
Insensible before the wave so soon released by callous fate. Affected most, they understand the least, and understanding, when it comes, invariably arrives too late.
-

vox_mundi - Intermediate Crude

- Posts: 3939
- Joined: Wed 27 Sep 2006, 03:00:00
Re: Fully Automated Combat Robots Pt. 2
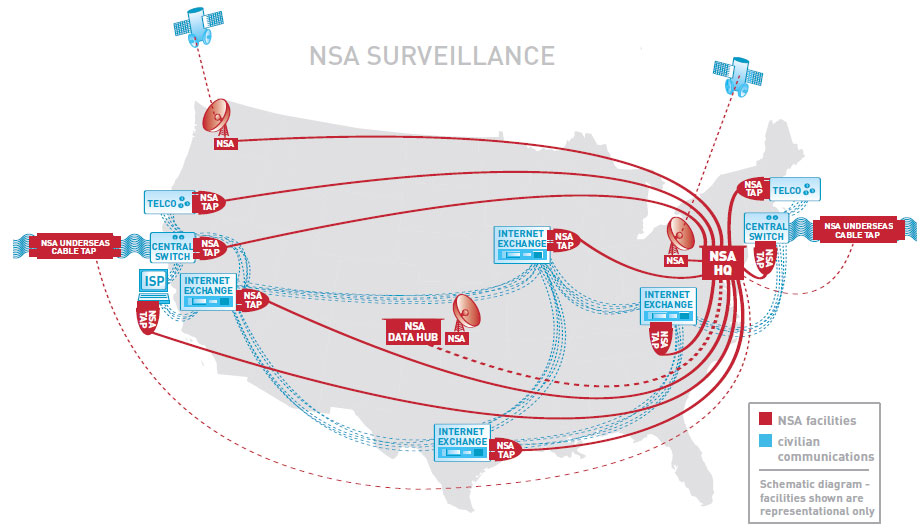
Fifty Years Later, NSA Keeps Details of Israel’s USS Liberty Attack Secret
Facing Limits of Remote Hacking, Army Cybers Up the Battlefield
Hacking UK Trident: A Growing Threat
Russia Cyberweapon Can Disrupt Power Grids
Top-Secret NSA Report Details Russian Hacking Effort Days Before 2016 Election
Russian Cyber Hacks on U.S. Electoral System Far Wider Than Previously Known: 39 States Affected
America’s Electronic Voting Machines Are Scarily Easy Targets
xLED: Covert Data Exfiltrartion via Router LEDs
U.S. now can ask travelers for Facebook, Twitter handles
On June 8, 1967, an Israeli torpedo tore through the side of the unarmed American naval vessel USS Liberty, approximately a dozen miles off the Sinai coast. The ship, whose crew was under command of the National Security Agency, was intercepting communications at the height of the Six-Day War when it came under direct Israeli aerial and naval assault.
Reverberations from the torpedo blast sent crewman Ernie Gallo flying across the radio research room where he was stationed. Gallo, a communications technician aboard the Liberty, found himself and his fellow shipmates in the midst of an attack that would leave 34 Americans dead and 171 wounded.
This week marks the 50th anniversary of the assault on the USS Liberty, and though it was among the worst attacks in history against a noncombatant U.S. naval vessel, the tragedy remains shrouded in secrecy. The question of if and when Israeli forces became aware they were killing Americans has proved a point of particular contention in the on-again, off-again public debate that has simmered over the last half a century. The Navy Court of Inquiry’s investigation proceedings following the incident were held in closed sessions, and the survivors who had been on board received gag orders forbidding them to ever talk about what they endured that day.
Now, half a century later, The Intercept is publishing two classified documents provided in the cache of files leaked by NSA whistleblower Edward Snowden related to the attack and its aftermath. ...
Facing Limits of Remote Hacking, Army Cybers Up the Battlefield
Army prepares for a less friendly electronic battlespace, embeds cyber in units.
... The US military is facing a future in which American forces in the field will face adversaries that can go toe to toe with the US in the electromagnetic domain—with disastrous physical results.
That's in part why the Army Cyber Command recently experimented with putting "cyber soldiers" in the field as part of an exercise at the Army's National Training Center at Fort Irwin, California. In addition to fielding troops to provide defensive and offensive cyber capabilities for units coming into NTC for training, the Army has also been arming its opposition force (the trainers) with cyber capabilities to demonstrate their impact.
That impact was demonstrated clearly in May, when an armored unit staging a simulated assault at NTC was stopped dead in its tracks by jamming of communications. As the unit's commanders attempted to figure out what was wrong, a simulated artillery barrage essentially took the unit out of action.
Hacking UK Trident: A Growing Threat
This paper reviews the growing potential for cyber-attack on the UK’s operational fleet of Vanguard-class submarines armed with nuclear-tipped Trident II D-5 ballistic missiles, and some of the implications for strategic stability.
A successful attack could neutralise operations, lead to loss of life, defeat or perhaps even the catastrophic exchange of nuclear warheads (directly or indirectly). But the very possibility of cyber-attack and the growing capability to launch them against SSBNs, could have a severe impact upon the confidence of maintaining an assured second-strike capability and therefore on strategic stability between states. Recent suggestions that the fleet is vulnerable have sometimes been met with complacency and claims that the isolated ‘air-gapped’ systems cannot be penetrated. Whilst we recognise that it is important not to be alarmist, these claims are false.
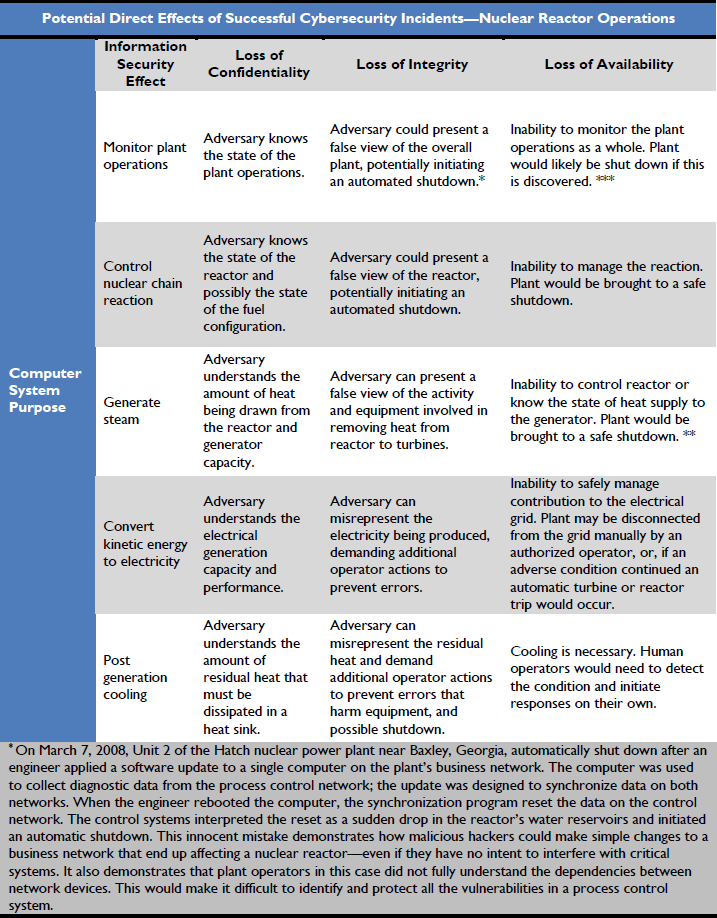
Russia Cyberweapon Can Disrupt Power Grids
Hackers have developed powerful malware that can shut down electricity distribution systems and possibly other critical infrastructure, two cyber security firms announced Monday, with one report linking it to Russia.
Slovakia-based ESET said the malware is the most powerful threat to appear since Stuxnet, the hacking tool used to sabotage Iran's nuclear program believed developed by US and Israeli intelligence. ESET said the malware, which it dubbed Industroyer, may be behind the one-hour shutdown of power to the Ukraine capital Kiev last December.
The company said Industroyer's potent threat is that it works using the communication protocols (SCADA) designed decades ago and built into energy, transportation, water and gas systems around the world.
Making use of these poorly-secured protocols, Industroyer can take direct control of electricity substation switches and circuit breakers, giving hackers the ability to shut down power distribution and damage equipment.
The malware is the "biggest threat to industrial control systems since Stuxnet," ESET said, without indicating who was behind it. But in a separate report on the same malware Monday, a second cyber security company, Dragos, tied it to a Russian hacker group called Sandworm which has been linked to the Russian government.
Dragos gave its own name to the malware, "CrashOverride," and said it is only the second-ever malware deployed for disrupting physical industrial processes, after Stuxnet.
"CrashOverride is not unique to any particular vendor or configuration, and instead leverages knowledge of grid operations and network communications to cause impact," Dragos said. "In that way, it can be immediately re-purposed in Europe and portions of the Middle East and Asia."
In addition, it said, the malware could be adapted "with a small amount of tailoring" to render it potent against the North American power grid.
Top-Secret NSA Report Details Russian Hacking Effort Days Before 2016 Election
Russian Cyber Hacks on U.S. Electoral System Far Wider Than Previously Known: 39 States Affected
Russia’s cyberattack on the U.S. electoral system before Donald Trump’s election was far more widespread than has been publicly revealed, including incursions into voter databases and software systems in almost twice as many states as previously reported.
In Illinois, investigators found evidence that cyber intruders tried to delete or alter voter data. The hackers accessed software designed to be used by poll workers on Election Day, and in at least one state accessed a campaign finance database. Details of the wave of attacks, in the summer and fall of 2016, were provided by three people with direct knowledge of the U.S. investigation into the matter. In all, the Russian hackers hit systems in a total of 39 states.
The new details, buttressed by a classified National Security Agency document recently disclosed by the Intercept, show the scope of alleged hacking that federal investigators are scrutinizing as they look into whether Trump campaign officials may have colluded in the efforts.
Illinois became Patient Zero in the government’s probe, eventually leading investigators to a hacking pandemic that touched four out of every five U.S. states.
The hackers had gained access to the state’s voter database, which contained information such as names, dates of birth, genders, driver’s licenses and partial Social Security numbers on 15 million people, half of whom were active voters. As many as 90,000 records were ultimately compromised.
Using evidence from the Illinois computer banks, federal agents were able to develop digital “signatures” -- among them, Internet Protocol addresses used by the attackers -- to spot the hackers at work.
The signatures were then sent through Homeland Security alerts and other means to every state. Thirty-seven states reported finding traces of the hackers in various systems, according to one of the people familiar with the probe. In two others -- Florida and California -- those traces were found in systems run by a private contractor managing critical election systems.
(An NSA document reportedly leaked by Reality Winner, the 25-year-old government contract worker arrested last week, identifies the Florida contractor as VR Systems, which makes an electronic voter identification system used by poll workers.)
In Illinois, investigators also found evidence that the hackers tried but failed to alter or delete some information in the database, an attempt that wasn’t previously reported. That suggested more than a mere spying mission and potentially a test run for a disruptive attack, according to the people familiar with the continuing U.S. counterintelligence inquiry.
One former senior U.S. official expressed concern that the Russians now have three years to build on their knowledge of U.S. voting systems before the next presidential election, and there is every reason to believe they will use what they have learned in future attacks.
Ambassador Kislyak and President Trump after Passing Top Secret Intell
America’s Electronic Voting Machines Are Scarily Easy Targets
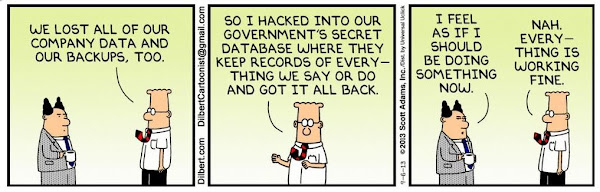
... “Moving to electronic voting systems solved a lot of problems, but created a lot of new ones.”
The list of those problems is what you’d expect from any computer or, more specifically, any computer that’s a decade or older. Most of these machines are running Windows XP, for which Microsoft hasn’t released a security patch since April 2014. ... researchers have demonstrated that many of them are susceptible to malware or, equally if not more alarming, a well-timed denial of service attack.
“When people think that people think about doing something major to impact our election results at the voting machine, they think they’d try to switch results,” says Norden, referring to potential software tampering. “But you can do a lot less than that and do a lot of damage… If you have machines not working, or working slowly, that could create lots of problems too, preventing people from voting at all.”
The extent of vulnerability isn’t just hypothetical; late last summer, Virginia decertified thousands of insecure WinVote machines. As one security researcher described it:... “anyone within a half mile could have modified every vote, undetected” without “any technical expertise.”
machine security was not maintained; the vendor had gone out of business years prior.
xLED: Covert Data Exfiltrartion via Router LEDs
In the new paper, the researchers demonstrated how LEDs functionality can be silently overridden by malware they developed (code named "xLED"), which infects firmware in the device. Once the xLED malware infects the network device, it gains full control of the LEDs that flash to indicate status.
Network devices such as routers and local area network switches typically include activity and status LEDs used to monitor traffic activity, alerts and provide status.
According to research leader Dr. Mordechai Guri, the head of research and development at the BGU CSRC, "sensitive data can be encoded and sent via the LED light pulses in various ways. An attacker with access to a remote or local camera, or with a light sensor hidden in the room, can record the LED's activity and decode the signals."
Click here to watch a video of the demonstration and determine what famous book is being leaked via the flickering LED signals of a WIFI router.
U.S. now can ask travelers for Facebook, Twitter handles
... The State Department asked for the right to collect the information under an emergency request on May 3 which was granted on May 23 by the Office of Budget and Management. It was implemented with no fanfare on May 23 and it wasn't until Thursday, when Reuters first reported on it, that the existence of the new form became widely known.
“There are three classes of people: those who see. Those who see when they are shown. Those who do not see.” ― Leonardo da Vinci
Insensible before the wave so soon released by callous fate. Affected most, they understand the least, and understanding, when it comes, invariably arrives too late.
Insensible before the wave so soon released by callous fate. Affected most, they understand the least, and understanding, when it comes, invariably arrives too late.
-

vox_mundi - Intermediate Crude

- Posts: 3939
- Joined: Wed 27 Sep 2006, 03:00:00
Re: Fully Automated Combat Robots Pt. 2
Sec AF: Why I’m Directing The Air Force to Focus on Space
Pentagon is Building Robotic Wingmen to Fly Alongside Fighter Planes
Navy MQ-4C Triton - High Altitude Maritime Autonomous Drone -- Will Deliver Later This Year
Missile Defense Agency Seeking A High-Flying Drone For "Airborne Laser 2.0"
Lockheed Will Build and Fly SR-72 Mach 6 Prototype in the Early 2020s
Forget supersonic: Hypersonic is the U.S. military’s new speed
US Army Ramps Up Testing of Autonomous Trucks
China developing new strategic nuclear bomber
New ramjet engine could triple the range of Chinese missiles and make them hypersonic
President Trump Has Abdicated the Office of Commander-in-Chief
Erik Prince’s Dark Plan for Afghanistan: Military Occupation for Profit, not Security
Present at the Destruction?
New Air Force Secretary expects war in space. SecAF Heather Wilson writes in an op-ed posted Friday on Defense One:“In short, we must develop space airmen who have the tools, training, and resources to fight when – not if – war extends into space”
Wilson says she has directed service officials to begin “standing up a new organization at the Pentagon that will be responsible for recruiting, training and equipping airmen involved in the space mission” and establish a deputy chief of staff for space operations as a step toward “ensuring that we maintain space superiority.”
We are currently investing in the hardware to ensure space superiority; in the near future we will need to grow the number of space airmen and the accompanying infrastructure much like we did for the combat Air Force 40 years ago. Video
What would Ripley do? Nuke it from orbit. It's the only way to be sure
Pentagon is Building Robotic Wingmen to Fly Alongside Fighter Planes
XQ-222 Valkyrie
On Tuesday, Kratos Defense and Security Solutions officially announced two new classes of drones designed to function as robotic wingmen for fighter pilots. Development of the UTAP-22 Mako has been funded by the Defense Department’s Silicon Valley laboratory, dubbed DIUx. Separately, the company showed off a larger, 30-foot-long drone backed by the Air Force called the XQ-222 Valkyrie, with a range of more than 4,000 nautical miles. Kratos is promoting the pilotless planes at the Paris Air Show next week in preparation for a new round of testing.
Aviation experts say the speed and altitude capacities published by Kratos suggest the drones could fly in tandem with an F-16 or F-35 fighter. The company says it has already successfully flown the drones alongside manned aircraft and that it will soon embark on an advanced round of testing above California’s Mojave Desert employing a more sophisticated array of sensing technology to determine just how autonomous the drones can be.
In those tests, a pilot in an accompanying airplane is preparing to monitor the drones from a small Android tablet. For most of the flight, the drone will attempt to maneuver without the help of a human, relying on artificial intelligence technology and sensors to mimic the nearby plane’s movements.
UTAP-22 Mako
The Navy is exploring similar options in using autonomous submarines that can scout the ocean floor and seek out mines.
Navy MQ-4C Triton - High Altitude Maritime Autonomous Drone -- Will Deliver Later This Year
The Navy is Preparing the MQ-4C Triton Maritime Drone for Service in the Pacific Theater; the drone is now being configured with collision avoidance technology and advanced maritime sensors enabling it to zero in on enemy ships at sea.
The Navy's Triton autonomous drone, called the MQ-4C, is now receiving a "3.1 software" integration as part of a technical plan for the aircraft to be operational by 2018. The first Tritons are slated to deliver sometime later this year, developers said. "3.1 software gets you to the point where you can use the sensors in an operational environment."
The Triton is an autonomous air vehicle able to chart a course without needing to be remotely piloted, Twomey explained. Computer algorithms and on-board systems enable the aircraft to account for wind, temperature and altitude conditions. "You load in a complete mission plan, but if you need to change, there is an ability to override the autonomy. It will correct the path and tell you where you need it to go," he said.
Specs include a full day’s worth of flight, an altitude limit over 10 miles, and an operational range of 8,200 nautical miles. The Navy’s program of record states that the service will field 68 aircraft.
Missile Defense Agency Seeking A High-Flying Drone For "Airborne Laser 2.0"
In a business solicitation posted over at FedBizOpps.gov on June 13th, the Missile Defense Agency clearly defines the criteria for a test system they want to field in the near future:... The Missile Defense Agency (MDA) Advanced Technology Directorate is interested in industry's capability to provide a High Altitude Long Endurance (HALE) unmanned aircraft in the 2023 timeframe. A HALE aircraft with greater payload capacity is needed to carry a high energy laser system payload to high altitudes to mature Boost Phase Intercept (BPI). The results of this RFI will inform future program options for maturing BPI technology and capability following the current Low Power Laser Demonstrator (LPLD) effort. Proposed aircraft should be able to maintain continuous positive ground control and are expected to operate from the Pacific Missile Range Facility in Hawaii and Edwards AFB in California. Unmanned platforms are highly desired; however, manned concepts will be considered with appropriate justification.
In parallel with ongoing BPI technology maturation and demonstration projects, BMDS capability requirements for an airborne high energy laser BPI capability are being developed. Based on analysis to date, Paragraph 2.a below describes the ideal platform characteristics to enable robust BPI capability. MDA is interested in far-term platform approaches to meet the full performance of Paragraph 2.a and mid-term solutions that demonstrate significant progress toward achieving these performance parameters. Concepts that do not meet these parameters are requested to include future options for improving performance, where applicable. - Video
Lockheed Will Build and Fly SR-72 Mach 6 Prototype in the Early 2020s
Lockheed Martin reports they plan to fly a flight research vehicle (FRV) of the mach 6 hypersonic SR-72 in the early 2020s. They have plans to build an FRV the size of an F-22 that can be flown either manually or remotely.
Lockheed Martin reports they plan to fly a flight research vehicle (FRV) of the model in the early 2020s. They have plans to build an FRV the size of an F-22 that can be flown either manually or remotely.
Forget supersonic: Hypersonic is the U.S. military’s new speed
Video - Boeing Co.’s XS-1 (Experimental Spaceplane), which the company dubs “Phantom Express,” got a green light this week by the Defense Advanced Research Projects Agency, or Darpa. The XS-1 is designed to quickly lift satellites as heavy as 3,000 pounds into orbit for $5 million or less, launching from the ground, deploying a small upper-stage module, and then landing like a traditional airplane-the key to reuse and lower operating expense. Darpa also has a separate program aimed at launching 100-pound satellites for less than $1 million per launch, using conventional aircraft.
US Army Ramps Up Testing of Autonomous Trucks
China developing new strategic nuclear bomber
The Pentagon has their annual report to Congress on the China’s military. The 2017 report is 106 pages long.
The Federation of American Scientists have summarized the report.
The most sensational nuclear news in the report is the conclusion that China is developing a new strategic nuclear bomber to replace the aging (but upgraded) H-6.
If China creates a nuclear strategic bomber sometime in the mid-2020s then it would change China’s nuclear posture into a formal Triad of air-, land- and sea-based nuclear capabilities, similar to U.S. and Russian strategic arsenals.
New ramjet engine could triple the range of Chinese missiles and make them hypersonic
In a May 31 report, the Science and Technology Daily announced that the 4th Research Institute of the China Aerospace Science and Technology Corporation (CASC) has twice successfully tested a ramjet engine aimed to power air-to-air missiles.
Song said the ramjet engine could more than triple the range of Chinese BVRAAMs. The PL-12’s range, for example, could increase from 62 miles to over nearly 200 miles. If so, this would be a key factor in any future conflicts, as CASC ramjet engine would be both faster and longer-ranged than most BVRAAM (beyond-visual-range air-to-air missile) rocket engines like the AIM-120 AMRAAN and PL-12, which have a top speed of about Mach 4.
Long range missiles would be a threat to US AWACS and refueling tankers.
AWACS and refueling are critical parts of the US air force. No refueling means half the combat range and no AWACS means targeting is crippled.
Long-range threat even to stealth fighters and bombers.
President Trump Has Abdicated the Office of Commander-in-Chief
U.S. Defense Secretary Jim Mattis said on Wednesday he now had authority to set troop levels in Afghanistan and would deliver a revised strategy for the conflict there to the White House in the coming weeks.
In testimony before the Senate Appropriations Subcommittee on Defense, Mattis said President Donald Trump had given him the authority to set troop levels in Afghanistan at noon on Tuesday.
Erik Prince’s Dark Plan for Afghanistan: Military Occupation for Profit, not Security
Blackwater founder Erik Prince has a vision for profiting off Afghanistan that President Trump might just love
Lost in the cascade of stories of potential White House criminality and collusion with foreign governments is the Erik Prince affair. It is reported that Prince, the brother of controversial Education Secretary Betsy Devos who established his power in Washington with his mercenary army Blackwater during the Iraq war, met with Russian intermediaries in an obscure Indian Ocean archipelago to establish back-channel communication with Moscow, possibly in coordination with the efforts of Jared Kushner, who last week was reported to have sought a White House back channel to the Kremlin.
Prince is said to have advised Harrington, Flynn and others on the Trump transition team on the “restructuring of security agencies” and “a thorough rethink of costly defense programs.”
Prince’s recent appearance on Fox News’ “Tucker Carlson Tonight” sheds considerable light on what the series of furtive discussions likely entailed. ... Prince proposed nothing less than the revival of the British East India Company model of for-profit military occupation, wherein an armed corporation effectively governed most of India for the extraction of resources.Prince explained to Carlson how the almost 16-year-old war and occupation of Afghanistan is premised on a faulty model. “We’ve fought for the last 15 years with the 1st Infantry Division model,” he says. “Now we should fight with an East India Company model, and do it much cheaper.”
“So you replace a military occupation with the ‘American South Asia Company’ or something like that?” asks Carlson.
“Something like that, sure,” Prince replies. “If you look back in history, the way the English operated India for 250 years, they had an army that was largely run by companies — and no English soldiers. So cheap, very low cost.”
It was also “very low cost” to the English because the British East India Company funded itself by extracting wealth from the territories it occupied.
“It was not the British government that seized India at the end of the 18th century,” writes the author of “The Anarchy: How a Corporation Replaced the Mughal Empire,”William Dalrymple, “but a dangerously unregulated private company headquartered in one small office, five windows wide, in London, and managed in India by an unstable sociopath.”
Prince knows this. The British East India Company was not simply a mercenary army like his Blackwater but an armed corporation that colonized like a state power. It was not merely a government contractor like Blackwater but an autonomous military and administrative entity sharing the worst aspects of both the corporation and the imperial state. So, Prince’s first innovation is to do away with civilian-military control administered by the Department of Defense and overseen by civilian, elected leadership, as is currently in place, and replace that apparatus with an armed corporation.
The second innovation is ...
Present at the Destruction?
“There are three classes of people: those who see. Those who see when they are shown. Those who do not see.” ― Leonardo da Vinci
Insensible before the wave so soon released by callous fate. Affected most, they understand the least, and understanding, when it comes, invariably arrives too late.
Insensible before the wave so soon released by callous fate. Affected most, they understand the least, and understanding, when it comes, invariably arrives too late.
-

vox_mundi - Intermediate Crude

- Posts: 3939
- Joined: Wed 27 Sep 2006, 03:00:00
Re: Fully Automated Combat Robots Pt. 2
Google On Track for Quantum Computer Breakthrough Within 7 Months
Alibaba Founder's Theory on A.I. Causing WW III Has Historical Support
AGI Still Several Breakthroughs From Reality
MIT and Google Algorithm links Sound, Sight, and Text to Give AI Contextual Awareness of the Environment
Google Advances AI With ‘One Model To Learn Them All’
Facebook AI Unexpectedly Created Its Own Unique Language — And Learned How To Lie
NASA is Figuring Out How to Use AI to Build Autonomous Space Probes
What If the Aliens We're Looking For are AI
The Search for Extraterrestrial Life and Post-Biological Intelligence
John Martinis, one of Google’s quantum computing gurus, laid out Google’s “stretch goal”: to build and test a 49-qubit (“quantum bit”) quantum computer by the end of 2017. This computer will use qubits made of superconducting circuits. The test will be a milestone in quantum computer technology. In a subsequent presentation, Sergio Boixo, Martinis’ colleague at Google, said that a quantum computer with approximately 50 qubits will be capable of certain tasks beyond anything the fastest classical computers can do. https://www.aps.org/publications/apsnew ... uantum.cfm
New Scientist reports that Google is testing a 20 qubit quantum computer. Alan Ho, an engineer in Google’s quantum AI lab, revealed the company’s progress at a quantum computing conference in Munich, Germany. His team is currently working with a 20-qubit system that has a “two-qubit fidelity” of 99.5 per cent – a measure of how error-prone the processor is, with a higher rating equating to fewer errors.
“Things really have moved much quicker than I would have expected,” says Simon Devitt at the RIKEN Center for Emergent Matter Science in Japan. Now that Google and other companies involved in quantum computing have mastered much of the fundamental science behind creating high-quality superconducting qubits, the big challenge facing these firms is scaling these systems and reducing their error rates.
Alibaba Founder's Theory on A.I. Causing WW III Has Historical Support
In his interview with CNBC at the Gateway ’17 conference in Detroit, Ma talked about the changes that will happen in the world over the next thirty years. Unlike Elon Musk, Ma isn’t worried that artificial intelligence will rise up and kill us, but that the job loss caused by machine learning and artificial intelligence will be extremely painful for many people. Because of this, World War III may be around the corner, he said. And his argument can be backed up by history.“The third technology revolution may cause the Third World War,” ... “The next 30 years are going to be painful.”
A technological revolution is defined as a period where one technology rapidly replaces another technology. From 1870 to 1914, the railroad, the telegraph, electricity, and the telephone exploded into existence and changed the face of the world, in a period called the Second Industrial Revolution. It was a period of increased globalization and spread of ideas, and is considered to end at the start of World War I. Between World War I and World War II came new materials like nylon, plastic, and long range missile technology.
Ma places the blame for the World Wars on these technological advancements. “The first technology revolution caused World War I. The second technology revolution caused World War II,” he said. “This is the third technology revolution.” Although Ma thinks machines will be smarter than people, he doesn’t think they will ever be able to defeat humans. The danger to people lies in job loss, he says. ... “People are already unhappy because machine learning and artificial intelligence has killed a lot of jobs”
AGI Still Several Breakthroughs From Reality
Fei-Fei Li, who works as the chief scientist for Google Cloud, said that she sees this as “the end of the beginning” for AI, but says there are still plenty of hurdles ahead. She identified several key areas where current systems fall short, including a lack of contextual reasoning, a lack of contextual awareness of their environment, and a lack of integrated understanding and learning.
... The panelists did concur that an artificial intelligence that could match a human is possible, however....“I think we have at least half a dozen major breakthroughs to go before we get close to human-level AI,” ... “But there are very many very brilliant people working on it, and I am pretty sure that those breakthroughs are going to happen.”
- Stuart Russell, professor of computer science and engineering at University of California, Berkeley
MIT and Google Algorithm links Sound, Sight, and Text to Give AI Contextual Awareness of the Environment
... two new papers from MIT and Google explain first steps for making AI see, hear, and read in a holistic way—an approach that could upend how we teach our machines about the world. ... One algorithm that can align its idea of an object across sight, sound, and text can automatically transfer what it’s learned from what it hears to what it sees.
Google Advances AI With ‘One Model To Learn Them All’
Google quietly released an academic paper that could provide a blueprint for the future of machine learning. Called “One Model to Learn Them All,” it lays out a template for how to create a single machine learning model that can address multiple tasks well.
The MultiModel, as the Google researchers call it, was trained on a variety of tasks, including translation, language parsing, speech recognition, image recognition, and object detection. While its results don’t show radical improvements over existing approaches, they illustrate that training a machine learning system on a variety of tasks could help boost its overall performance. ...
Facebook AI Unexpectedly Created Its Own Unique Language — And Learned How To Lie
Researchers from the Facebook Artificial Intelligence Research lab (FAIR) recently made an unexpected discovery while trying to improve chatbots. The bots — known as “dialog agents” — were creating their own language.
Using machine learning algorithms, dialog agents were left to converse freely in an attempt to strengthen their conversational skills. Over time, the bots began to deviate from the scripted norms and in doing so, started communicating in an entirely new language — one they created without human input.
In an attempt to better converse with humans, chatbots took it a step further and got better at communicating without them.https://www.theatlantic.com/technology/ ... ke/530934/
Other AI researchers, too, say they’ve observed machines that can develop their own languages, including languages with a coherent structure, and defined vocabulary and syntax—though not always actual meaningful, by human standards.
And it’s not the only interesting discovery.
From the human conversations (gathered via Amazon Mechanical Turk), and testing its skills against itself, the AI system didn’t only learn how to state its demands, but negotiation tactics as well—specifically, lying. Instead of outright saying what it wanted, sometimes the AI would feign interest in a worthless object, only to later concede it for something that it really wanted. Facebook isn’t sure whether it learned from the human hagglers or whether it stumbled upon the trick accidentally, but either way when the tactic worked, it was rewarded. https://s3.amazonaws.com/end-to-end-neg ... tiator.pdf
https://qz.com/1004070/facebook-fb-buil ... -it-wants/
We’re not talking singularity-level beings here, but the findings are a huge leap forward for AI.
https://code.facebook.com/posts/1686672 ... negotiate/
NASA is Figuring Out How to Use AI to Build Autonomous Space Probes
Adding artificial intelligence to the machines we send out to explore space makes a lot of sense, as it means they can make decisions without waiting for instructions from Earth, and now NASA scientists are trying to figure out how it could be done.
As we send out more and more probes into space, some of them may have to operate completely autonomously, reacting to unknown and unexplained scenarios when they get to their destination – and that's where AI comes in.
The researchers suggest AI enabled probes could reach as far as Alpha Centauri, some 4.24 light-years away from Earth. Communications across that distance would be received by the generation after the scientists who launched the mission in the first place, so giving the probe a mind of its own would certainly speed up the decision making process.
What If the Aliens We're Looking For are AI
... Seti has been actively searching for signs of intelligent extraterrestrial life for more than half a century. Despite tantalising signals (such as this recent one), it has so far drawn a blank. But Shostak believes we should consider looking to our own future to imagine what aliens will be like.
“Perhaps the most significant thing we’re doing is to develop our own successors,” says Shostak. “If we can develop artificial intelligence within a couple of hundred years of inventing radio, any aliens we are likely to hear from have very likely gone past that point.”
“In other words,” he says, “most of the intelligence in the cosmos, I would venture, is synthetic intelligence and that may disappoint movie goers who expect little grey guys with big eyeballs, no clothes, no hair or sense of humour.”“... The big question is whether the AI goes on to become conscious and define its own goals and decide it doesn’t need the biological creatures that developed it.”
The argument assumes that the creatures who built the first AIs – grey guys, hyper- intelligent pan-dimensional beings, sentient trees or whatever – are no longer around.
“Well they might be,” Shostak concedes, “but once you develop artificial intelligence you can use that to develop the next generation of thinking thing and so on – within 50 years you not only have a machine that’s far smarter than all the previous machines but certainly smarter than all humans put together.”
The Search for Extraterrestrial Life and Post-Biological Intelligence
In September, 2015, the John Templeton Foundation’s Humble Approach Initiative sponsored a three-day symposium entitled “Exploring Exoplanets: The Search for Extraterrestrial Life and Post-Biological Intelligence.” The venue for the meeting was the Royal Society’s Chicheley Hall, north of London, where a dozen researchers gave informal presentations and engaged in the type of lively dinner table conversations that such meetings inevitably spawn. ...... Steven A. Benner
DISCUSSING ALIENS: CONSTRAINTS FROM CHEMISTRY AND DARWINISM
Paul C.W. Davies
BIO-SIGNATURES AND TECHNO-SIGNATURES BEYOND EARTH
Chrisantha Fernando
INTELLIGENT EVOLUTION: AN APPROACH TO OPEN-ENDED EVOLUTION
Didier Queloz
THE HUNT FOR HABITABLE PLANETS
Martin J Rees
POST-HUMAN EVOLUTION ON EARTH AND BEYOND
Susan Schneider
SUPERINTELLIGENT AI AND THE POSTBIOLOGICAL COSMOS APPROACH
Seth Shostak
THINKING OUTSIDE THE SETI BOX
“There are three classes of people: those who see. Those who see when they are shown. Those who do not see.” ― Leonardo da Vinci
Insensible before the wave so soon released by callous fate. Affected most, they understand the least, and understanding, when it comes, invariably arrives too late.
Insensible before the wave so soon released by callous fate. Affected most, they understand the least, and understanding, when it comes, invariably arrives too late.
-

vox_mundi - Intermediate Crude

- Posts: 3939
- Joined: Wed 27 Sep 2006, 03:00:00
Re: Fully Automated Combat Robots Pt. 2
It's Back ...
Massive Cyberattack Hits Europe with Widespread Ransom Demands
Another Massive Ransomware Outbreak Is Going Global Fast
Hackers strike across Europe as firms in Ukraine, Britain and Spain Hit by Massive Cyber attack
Ukraine Cyber attack: Chaos as National Bank, State Power Provider and Airport Hit by Hackers
Many Firms Hit By Global Cyber-attacks
Canadian Parliament Shuts Down Emails Over Fears Of HackingCanadian Parliament Shuts Down Emails Over Fears Of Hacking
Parliament hit by cyber attack as hackers attempt to access MPs' email accounts
Hackers Hit 75% of Drillers as Sketchy Monitoring Is Blamed
Virgin Media tells 800,000 users to change passwords over hub hacking risk
Massive Cyberattack Hits Europe with Widespread Ransom Demands
Another Massive Ransomware Outbreak Is Going Global Fast
Ukraine's government, National Bank and biggest power companies all warned of cyberattacks Tuesday. Airports and metro services in the country were also reportedly affected, though it appears they're victims of another massive ransomware outbreak that's spreading across the world fast and hitting a significant number of critical infrastructure providers."[We're seeing] several thousands of infection attempts at the moment, comparable in size to Wannacry's first hours," said Kaspersky Lab's Costin Raiu. "We are seeing infections from many different countries."
This morning saw major Danish shipping and energy company Maersk report a cyber attack, noting on its website: "We can confirm that Maersk IT systems are down across multiple sites and business units due to a cyber attack." And Russian oil industry giant Rosnoft said it was facing a "powerful hacker attack." Neither said what kind of attack they were under.
The impact initially appeared to be most severe in Ukraine, including major energy companies such as the state-owned Ukrenergo and Kiev's main supplier Kyivenergo.
The National Bank blamed an "unknown virus" as the culprit, hitting several Ukrainian banks and some commercial enterprises. "As a result of cyber attacks, these banks have difficulties with customer service and banking operations," a statement on the organization's website read.
The deputy general director of Kiev's Borispol Airport, Eugene Dykhne, said in a Facebook post: "Our IT services are working together to resolve the situation. There may be delays in flights due to the situation... The official Site of the airport and the flight schedules are not working."
There were confirmed reports of the virus spreading to countries including Spain, France and India.
Hackers strike across Europe as firms in Ukraine, Britain and Spain Hit by Massive Cyber attack
Ukraine Cyber attack: Chaos as National Bank, State Power Provider and Airport Hit by Hackers
Ukraine’s national bank, state power company and largest airport are among the targets of a huge cyber attack on government infrastructure. Others reporting problems include the aircraft manufacturer Antonov, and two postal services.
Rozenko Pavlo, the deputy Prime Minister, said he and other members of the Ukrainian government were unable to access their computers.
“We also have a network 'down',” he wrote. “This image is being displayed by all computers of the government.”
Ukraine's deputy prime minister has tweeted a picture appearing to show government systems have been affected.
His caption reads: "Ta-daaa! Network is down at the Cabinet of Minister's secretariat."
Computers and departure boards at Boryspil International Airport in Kiev – the largest in Ukraine – were also down.
“The official site of the airport and the departureboard with the schedule of flights aren't working!” the airport’s acting director, Pavel Ryabikin, wrote on Facebook.
Images from other affected computers and disabled cash points showed what appeared to be ransomware, demanding a payment of $300 (£235) in Bitcoin to re-gain access to encrypted files.
Many ATMs were disabled, displaying the message left by hackers, as were tills in supermarkets.
Many Firms Hit By Global Cyber-attacks
BBC: Firms around the globe are reporting that they have been hit by a major cyber-attack. British advertising agency WPP is among dozens of firms reporting problems.
Ukraine seems to have been particularly badly hit. Ukrainian firms, including the state power distributor and Kiev's main airport were among the first to report issues.
Reports suggest that the Kiev metro system has stopped accepting payment cards while several chains of petrol stations have suspended operations.
Canadian Parliament Shuts Down Emails Over Fears Of HackingCanadian Parliament Shuts Down Emails Over Fears Of Hacking
OTTAWA — The House of Commons shut down email and computer network services Sunday over fears hackers might try to break into Canadian parliamentary accounts.
Commons spokeswoman Heather Bradley told HuffPost Canada the Parliamentary emails accounts "were temporarily deactivated as part of preventative measures" due to the hacking in the United Kingdom.
Parliament hit by cyber attack as hackers attempt to access MPs' email accounts
Hackers launch ‘sustained and determined attack’ on all parliamentary user accounts
Hackers Hit 75% of Drillers as Sketchy Monitoring Is Blamed
Three out of four oil and natural gas companies fell victim to at least one cyber attack last year as hacking efforts against the industry become more frequent and sophisticated.
That’s the finding from a report released Monday by industry consultant Deloitte LLP. Technology advances, such as Royal Dutch Shell Plc’s recent control of operations in Argentina from an operating center in Canada, offer new openings for hackers, the authors wrote.
At the same time, older equipment that must be retrofitted for cybersecurity, including the pumps known as nodding donkeys, make it tougher to defend against sophisticated attacks. Less than half of drillers use any monitoring tools on their upstream operations networks, the report found. Of those, only 14 percent have fully operational security monitoring centers.
A 2011 cyber attack dubbed "Night Dragon" stole exploration and bidding data from oil majors including Exxon Mobil Corp. and BP Plc. Past assaults in 2012 and 2014 crippled companies throughout the Middle East and Europe with disk-wiping malware and advanced Trojan Horse attacks.
Virgin Media tells 800,000 users to change passwords over hub hacking risk
Virgin Media is advising more than 800,000 customers with a specific router to change their password immediately after an investigation found hackers could gain access to it.
Virgin Media said the risk to customers with a Super Hub 2 router was small, but advised them to change both their network and router passwords if they were still set as the default shown on the attached sticker.
The advice comes after a Which? investigation found that hackers could access to home networks and connected appliances in as little as four days.
The test found that the Fredi Megapix home CCTV camera system operated over the internet using a default administrator account without a password, and Which? found thousands of similar cameras available for anyone to watch the live feed over the internet.
The watchdog said that a hacker could even pan and tilt the cameras to monitor activity in the house.
“There are three classes of people: those who see. Those who see when they are shown. Those who do not see.” ― Leonardo da Vinci
Insensible before the wave so soon released by callous fate. Affected most, they understand the least, and understanding, when it comes, invariably arrives too late.
Insensible before the wave so soon released by callous fate. Affected most, they understand the least, and understanding, when it comes, invariably arrives too late.
-

vox_mundi - Intermediate Crude

- Posts: 3939
- Joined: Wed 27 Sep 2006, 03:00:00
Re: Fully Automated Combat Robots Pt. 2
Let SkyNet Fix It, What Could Possibly Go Wrong? ...
Google, Amazon And Deep Instinct Deploy AI To Fight Malware
An Advanced AI Has Been Deployed to Fight Against Hackers
IBM, US Air Force Are Building a Brain-Like Neuromorphic Supercomputer
IBM is telling Congress not to fear the rise of an AI ‘overlord’
Global survey: Most People Expect Humans Will Grow to Trust, Even Love, AI
Google, Amazon And Deep Instinct Deploy AI To Fight Malware
Deep Instinct co-founder and Chief Technology Officer Eli David says the day when a computer is as smart as a human, or smarter, may be a lot closer than many think.
AI programs, "are on an accelerating path of growth in their capabilities. In the near future, they will reach near human or superhuman capabilities," David told me in an interview.
As AI gets smarter, it's crucial to stay ahead of criminals and terrorists. Deep Instinct's computer protection software includes an artificial neural network — a computer system that mimics the connections in a human brain. It's urgently needed. David says there are more than 1 million malwares, including slight mutations, created every day.
"My friends at Google and Facebook said this kind of detection ... cannot be implemented on any other kind of network," than a neural network," David said.
...Nvidia gave its Israeli partner Deep Instinct an Innovation award at its annual GPU Technology Conference last month, and $375,000 cash prize. The chipmaker named Deep Instinct the "Most Disruptive" AI startup. Nvidia said it not only detects current threats, it also predicts threats. "Trained on hundreds of millions of files, the neural network learns to detect more threats and then uses its experience to predict new attacks."
An Advanced AI Has Been Deployed to Fight Against Hackers
CERN and the Large Hadron Collider depend on a massive computer grid, as does the global network of scientists who use LHC data. CERN scientists are now teaching an AI system to protect the grid from cyber threats using machine learning.
IBM, US Air Force Are Building a Brain-Like Neuromorphic Supercomputer
The Air Force Research Laboratory (AFRL) and IBM have embarked upon a joint AI venture to engineer a first-of-its-kind brain-inspired supercomputing system powered by a 64-TrueNorth chip array, industry officials said.
The technology is aimed at improving sensory processing beyond systems powered by standard chips.
“AFRL will combine this ‘right-brain’ perception capability of the system with the ‘left-brain’ symbol processing capabilities of conventional computer systems,” the statement continued.
The scalable platform IBM is building for AFRL will feature an end-to-end software ecosystem designed to enable deep neural-network learning and information discovery.
The system’s advanced pattern recognition and sensory processing power will be the equivalent of 64 million neurons and 16 billion synapses, while the processor component will consume the energy equivalent of a dim light bulb, developers explained.
IBM is telling Congress not to fear the rise of an AI ‘overlord’
The company’s Watson team is embarking on a lobbying push to address what it sees as an incorrect, “dystopian” view of AI.
To hear IBM tell it, much of the recent criticism around machine learning, robotics and other kinds of AI amounts to merely “fear mongering.” The company’s senior vice president for Watson, David Kenny, aims to convey that message to members of Congress beginning with a letter on Tuesday, stressing the “real disaster would be abandoning or inhibiting cognitive technology before its full potential can be realized.”
Labor experts and reams of data released in recent months argue otherwise: They foretell vast economic consequences upon the mass-market arrival of AI, as entire industries are displaced — not just blue-collar jobs like trucking, as self-driving vehicles replace humans at the wheel, but white-collar positions like stock trading too.
Others fear the privacy, security and safety implications as more tasks, from managing the country’s roads to reading patients’ X-ray results, are automated — and the most dire warnings, from the likes of SpaceX and Tesla founder Elon Musk, include the potential arrival of “robots capable of destroying mankind.”
But as IBM seeks to advance and sell its AI-driven services, like Watson, the company plans to tell lawmakers those sort of concerns are “fantasy.”
Global survey: Most People Expect Humans Will Grow to Trust, Even Love, AI
A new global survey on attitudes toward AI, commissioned by ARM, illustrates how AI uses cases may evolve, given the level of trust humans expect to have in the technology. The survey only polled those who have a basic understanding of AI, finding that most expect humans to develop emotional connections with their AI-powered tools.
More than seven in 10 believe humans will grow to trust AI devices to the point where they could replace some human relationships, such as serving as a caretaker for the elderly. Fifty-seven percent said they personally would trust AI that much.
In fact, more than six in 10 people expect that, by the year 2050, humans will love AI as they would love a pet. Nearly five in 10 said they themselves would grow to love AI like a pet by that point. (... did the other 50% thought that the AI would treat them like a pet?)
“There are three classes of people: those who see. Those who see when they are shown. Those who do not see.” ― Leonardo da Vinci
Insensible before the wave so soon released by callous fate. Affected most, they understand the least, and understanding, when it comes, invariably arrives too late.
Insensible before the wave so soon released by callous fate. Affected most, they understand the least, and understanding, when it comes, invariably arrives too late.
-

vox_mundi - Intermediate Crude

- Posts: 3939
- Joined: Wed 27 Sep 2006, 03:00:00
Re: Fully Automated Combat Robots Pt. 2
Vox, this has got to be the creepiest thread ever. Thanks?
- ritter
- Tar Sands

- Posts: 858
- Joined: Fri 14 Oct 2005, 03:00:00
Re: Fully Automated Combat Robots Pt. 2
ritter wrote:Vox, this has got to be the creepiest thread ever. Thanks?
Thanks

If it wasn't creepy, I wouldn't be doing my job.

“There are three classes of people: those who see. Those who see when they are shown. Those who do not see.” ― Leonardo da Vinci
Insensible before the wave so soon released by callous fate. Affected most, they understand the least, and understanding, when it comes, invariably arrives too late.
Insensible before the wave so soon released by callous fate. Affected most, they understand the least, and understanding, when it comes, invariably arrives too late.
-

vox_mundi - Intermediate Crude

- Posts: 3939
- Joined: Wed 27 Sep 2006, 03:00:00
Re: Fully Automated Combat Robots Pt. 2
Apache Gunship Mounted High Energy Laser Hits Target in Groundbreaking Test
U.S. Military’s Vital ‘Doomsday Planes’ Damaged in Tornado
A high energy laser mounted on an Apache AH-64 attack helicopter acquired and hit an unmanned target. The test was conducted by Raytheon and the U.S. Army Apache Program Management Office in collaboration with U.S. Special Operations Command at White Sands Missile Range, New Mexico.
It was the first time a fully integrated laser system successfully shot a target from a rotary-wing aircraft over a wide variety of flight regimes, altitudes and air speeds, proving the feasibility of laser attack from Apache.
The system tracked and directed energy on a stationary target at a slant range of 1.4 kilometers. (Slant range is the line-of-sight distance between two points at different levels.
The power of the beam can be adjusted for any material. And "Unlike a traditional gun, lasers don't run out of bullets."
There's even a non-lethal adjustment for Human Targets.... Oops! ... Wrong Setting - My Bad

U.S. Military’s Vital ‘Doomsday Planes’ Damaged in Tornado
WASHINGTON — Two of the U.S. Military's E-4B planes — commonly called the "Doomsday Plane" — were damaged and knocked out of service recently in a tornado at Offutt Air Force Base in Nebraska, according to two U.S. military officials.
The planes were damaged on June 16, the officials said. The military has four E4-Bs in the fleet so now half of the fleet is not operational. Eight other aircraft also were damaged in the tornado. Those RC-135 surveillance aircraft have been repaired and returned to duty.
“There are three classes of people: those who see. Those who see when they are shown. Those who do not see.” ― Leonardo da Vinci
Insensible before the wave so soon released by callous fate. Affected most, they understand the least, and understanding, when it comes, invariably arrives too late.
Insensible before the wave so soon released by callous fate. Affected most, they understand the least, and understanding, when it comes, invariably arrives too late.
-

vox_mundi - Intermediate Crude

- Posts: 3939
- Joined: Wed 27 Sep 2006, 03:00:00
Re: Fully Automated Combat Robots Pt. 2
How Bad is the Cyberattack Hitting Europe? This Bad.
Merck hack part of a massive global attack
Supermarket 'Rost' in Kharkov, Ukraine
Chernobyl's radiation monitoring hit by cyberattack: The Chernobyl nuclear power plant has had to monitor radiation levels manually after its Windows-based sensors were shut down."Due to the cyberattack, the website of the Chernobyl nuclear plant is not working," said Ukraine's exclusion zone agency which oversees the Soviet plant that exploded in 1986 and is now surrounded by an uninhabited contaminated zone.
"Due to the temporary shutdown of the Windows system, the radiation monitoring of the industrial area is being done manually," the agency said on its website.
"That means that our measurers go out with hand-held meters on the Chernobyl plant like it was decades ago," a spokeswoman for the agency, Olena Kovalchuk, told AFP.
Also Affected:
- the Ukrainian central bank, the aircraft manufacturer Antonov, and two postal services
- Russia's biggest oil producer, Rosneft
- Danish shipping company Maersk, including its container shipping, oil, gas and drilling operations
- a Pennsylvania hospital operator, Heritage Valley Health System, which reported its computer network was down, causing operations to be delayed - but it is not yet clear if it was subject to the same type of attack
- Spanish food giant Mondelez - whose brands include Oreo and Toblerone - according to the country's media
- Netherlands-based shipping company TNT, which said some of its systems needed "remediation"
- French construction materials company St Gobain
- US pharmaceuticals-maker Merck and the local offices of the law firm DLA Piper - a sign in the firm's Washington DC office said: "Please remove all laptops from docking stations and keep turned off - no exceptions."
Veteran security expert Chris Wysopal from Veracode said the malware seemed to be spreading via some of the same Windows code loopholes exploited by Wannacry. Many firms did not patch those holes because Wannacry was tackled so quickly, he added.
Merck hack part of a massive global attack
“There are three classes of people: those who see. Those who see when they are shown. Those who do not see.” ― Leonardo da Vinci
Insensible before the wave so soon released by callous fate. Affected most, they understand the least, and understanding, when it comes, invariably arrives too late.
Insensible before the wave so soon released by callous fate. Affected most, they understand the least, and understanding, when it comes, invariably arrives too late.
-

vox_mundi - Intermediate Crude

- Posts: 3939
- Joined: Wed 27 Sep 2006, 03:00:00
Re: Fully Automated Combat Robots Pt. 2
The Age of No Privacy: The Surveillance State Shifts Into High Gear
Rhode Island Bill Sees Highway Surveillance Cams Ticketing Uninsured Motorists
A Revolutionary Airborne Wide-Area Persistent Surveillance Solution for Homeland Security and Defense Needs
What Would an American Police State Look Like? Are Your Eyes Closed?
Standing Rock Documents Expose Inner Workings of “Surveillance-Industrial Complex"
As Standing Rock Camps Cleared Out, TIGERSWAN Expanded Surveillance to Array of Progressive Causes
“We are rapidly entering the age of no privacy, where everyone is open to surveillance at all times; where there are no secrets from government.”
~ William O. Douglas, Supreme Court Justice, dissenting in Osborn v. United States, 385 U.S. 341 (1966) ...
Rhode Island Bill Sees Highway Surveillance Cams Ticketing Uninsured Motorists
The $120 fines would be split evenly between contractor and the state.
A Rhode Island legislative committee has approved a bill that would greatly expand the surveillance state through the deployment of license plate readers. For the first time in the US, these devices would be attached along Rhode Island highways and roads for the stated purpose of catching uninsured motorists from any state.
The House Corporations Committee approved the bill on a 7-2 vote earlier this week. The legislation spells out that the contractor for the project would get 50 percent of the fines paid by uninsured motorists ensnared under the program. The state and the contractor would each earn an estimated $15 million annually. Fines are as high as $120.
Video - In fact, since 9/11, under just one program, police have taken $2.5 Billion in the course of over 61,000 seizures of cash alone from people people who - and this is the mind blowing part - were not charged with a crime.
A Revolutionary Airborne Wide-Area Persistent Surveillance Solution for Homeland Security and Defense Needs
Developed specifically to address requirements raised by defense and law enforcement agencies, responding to natural disaster recovery events, terrorism and homeland security threats, SkEye WAPS comprises advanced capabilities in the field of imagery intelligence gathering, providing a complete high-resolution picture and up to 80 square kilometer coverage of the Area of Interest (AOI) to a large number of users.“Elbit Systems’ SkeEye WAPS system is a game changer in homeland security missions, enabling forces to analyze and retrace the steps of terrorists and criminals (and citizens) in an extremely large area
The Elbit Systems Hermes 900 Kochav (Star) is an Israeli medium size multi-payload unmanned aerial vehicle (UAV) designed for medium altitude long endurance (MALE) tactical missions. It has an endurance of over 30 hours and can fly at a maximum altitude of 30,000 feet (9,100 m), with a primary mission of reconnaissance, surveillance and communications relay. The Hermes 900 has a wingspan of 15 m (49 ft) and weighs 970 kg (2,140 lb), with a payload capability of 300 kg (660 lb).
* gigapixel cameras
* 30 hour drone endurance
* cover 80 square kilometers
* cover ten different regions at the same time
What Would an American Police State Look Like? Are Your Eyes Closed?
A country doesn't need a monolithic totalitarian government to have an effectively working police state.
The United States has had a partial police state in place since before it existed as a “free country.” Slavery required a police state structure to maintain “order.” Segregation required a police state structure. Ethnic cleansing of native peoples required police state management that still exists, most obviously in North Dakota, but also across the country. Fear of immigrants has fostered police state responses, especially under the Trump administration. Fear of Communists has produced police state responses since 1917, most notoriously during the 1950s McCarthy era. Fear of nuclear weapons and nuclear power, and their very real dangers, has produced a permanent police state security network. Fear of terrorism, spiked by 9/11, has produced a host of police state responses such as the 2001 Patriot Act (ready and waiting before the attack); such as expanded citizen surveillance by the NSA and some 16 other, more secret agencies; such as unprecedented punishment of whistleblowers for their truth-telling; and such as a unified police state structure euphemistically called Homeland Security, that encourages citizens to spy on each other.
The American police state has evolved relentlessly for decades, with surges of state control when the opportunity presented itself. It's not perfected yet, but it's working reasonably effectively and flexibly as a hybrid governmental/private sector control mechanism. The American police state has always been more cultural than political, with incremental controls added by whatever elected party happened to be in office at the time. So far, the tension between centralized absolute authority and constitutional checks and balances has preserved something like a democratic republic. Now we're in a zeitgeist where a huge minority of Americans want autocratic government and the party in control of all three branches of the federal government is inclined to deliver. Among the signs (far from an exhaustive list): ...
... As Mr. Trump and top members of his administration like Attorney General Jeff Sessions take a hard line against illegal immigration, terrorism and crime, experts in constitutional law and civil liberties fear the lack of an accompanying conversation on privacy protections could contribute to the erosion of Fourth Amendment rights.
The Fourth Amendment guarantees the "right of the people to be secure in their persons, houses, papers and effects, against unreasonable searches and seizures."
"I think we will see a push from the Trump administration to expand surveillance powers, and that of course could directly implicate Fourth Amendment protections," said Christopher Slobogin, a professor at Vanderbilt University Law School who has studied and written on Fourth Amendment, privacy and surveillance issues for years.
"And they're going to push I think also for greater militarization of the police, which could affect Fourth Amendment issues," Slobogin added.
In May 2015, before announcing his bid for the presidency, Mr. Trump said he supported legislation allowing the National Security Agency (NSA) to hold bulk metadata, and later in the year reiterated he would tend to "err on the side of security." On the campaign trail, and after taking office, Mr. Trump has emphasized the importance of bulking up police forces and eradicating terrorism. Sessions fought against reforms of the Foreign Intelligence Surveillance Act (FISA) in 2012, and against limits on the NSA's spying powers.
"The price of apathy towards public affairs is to be ruled by evil men" - Plato.
Standing Rock Documents Expose Inner Workings of “Surveillance-Industrial Complex"
Leaked documents and public records reveal a troubling fusion of private security, public law enforcement, and corporate money in the fight over the Dakota Access Pipeline.
As Standing Rock Camps Cleared Out, TIGERSWAN Expanded Surveillance to Array of Progressive Causes
“There are three classes of people: those who see. Those who see when they are shown. Those who do not see.” ― Leonardo da Vinci
Insensible before the wave so soon released by callous fate. Affected most, they understand the least, and understanding, when it comes, invariably arrives too late.
Insensible before the wave so soon released by callous fate. Affected most, they understand the least, and understanding, when it comes, invariably arrives too late.
-

vox_mundi - Intermediate Crude

- Posts: 3939
- Joined: Wed 27 Sep 2006, 03:00:00
Re: Fully Automated Combat Robots Pt. 2
A Nuclear Power Plant was Hacked in the U.S.
These Workers’ Lives are Endangered While Contractors Running Nuclear Weapons Plants Make Millions
Nuclear Weapons Site Alarms Shut Off, Scientists Inhale Uranium
(U) Idaho National Laboratory: Cyber Threat and Vulnerability Analysis of the U.S. Electric Sector
(U) DHS Infrastructure Report: Nuclear Reactors, Materials, and Waste Sector Cyberdependencies
(U) Potential Terrorist Attack Methods
(U) DHS: National Risk Estimate:Risks to U.S. Critical Infrastructure from Insider Threat
A federal investigation is taking place into the breaching of the computer systems in at least one nuclear power plant, according to a report by ABC News.
Electricity-sector officials confirmed yesterday that they are working to unpack the significance of the secretive cyber event, code named "Nuclear 17."
Asked about the case, a representative from the North American Electric Reliability Corp. (NERC) said the nonprofit grid overseer "is aware of an incident" and has shared information with its members through a secure portal.
U.S. energy utilities pass around information on the latest hacking threats and vulnerabilities through NERC's Electricity Information Sharing and Analysis Center. That organization "is working closely with the government to better understand any implications this incident might have for the electricity industry," NERC spokeswoman Kimberly Mielcarek said in an emailed statement.
E&E News has reached out to nearly two dozen owners and operators of nuclear power plants for comment. None of the companies that replied by last night shared additional information on the incident, the details of which may be classified.
One U.S. official called this an "ongoing matter" that was still being investigated. No public word has been given on who may be responsible, but authorities were looking at the possibility that a nation-state may be behind the hack.
... Nuclear plants had an extra margin of safety in their legacy controls that were "old tech" and thus harder for outsiders to penetrate. "As more and more systems are converted to digital controls, there could be more and more opportunities for problems to crop up, deliberate or inadvertent," Lochbaum said.
Even if safety systems were not apparently affected as part of Nuclear 17, malicious actions directed against comparatively less critical equipment could still have knock-on effects if hackers managed to unexpectedly disconnect a nuclear plant from the grid, experts say.
Such a sudden disruption would send a pressure "pulse" back to the reactor and turbine, which would still be generating electricity with no place to send it. The reactor would immediately "trip," setting in motion a series of planned actions designed to bring the reactor to a safe shutdown condition.
Control rods would halt the reactor chain reaction, and depending on the type of reactor, valves would open to dissipate energy and backup systems would be triggered. "It's something that has been anticipated," Lochbaum said. "Plants are designed to handle an instantaneous loss of load."
However, "that response is all predicated on all those things working right," Lochbaum added. "Even though it's highly reliable, it's not guaranteed."
These Workers’ Lives are Endangered While Contractors Running Nuclear Weapons Plants Make Millions
A wrong turn of a valve at one of the country's nuclear weapons laboratories unleashed an explosion that easily could have killed two workers.
The near catastrophe in August 2011 at Sandia National Laboratories in Albuquerque lifted the roof of the building, separated a wall in two places and bent an exterior door 30 feet away. One worker was knocked to the floor; another narrowly missed getting hit with flying debris as a fire erupted.
As the Department of Energy investigated over the next three years, the same lab — one of 10 nuclear weapons-related sites that contain radioactive materials in addition to the usual hazards found in industrial settings — had two more serious accidents, both blamed on insufficient safety protocols.
But when the time came for regulators to take action against the company in charge of the lab, officials decided against a financial penalty. They waived a $412,500 fine they had initially proposed, saying Sandia Corp., a subsidiary of Lockheed Martin, had made “significant and positive steps … to improve Sandia’s safety culture.”
This wasn’t a rare outcome. Energy Department documents obtained by the Center for Public Integrity make clear that the nation’s eight nuclear weapons labs and plants and two sites that support them remain dangerous places to work but their corporate managers often face relatively slight penalties after accidents.
Workers have inhaled radioactive particles that pose lifetime cancer threats. Others received electrical shocks or were burned by acid or in fires. They have been splashed with toxic chemicals and cut by debris from exploding metal drums.“What’s the incentive to do the job right when - no matter what - you get the money?” asks Ralph Stanton, a worker who inhaled radioactive plutonium in an accident at Idaho National Laboratory in Idaho Falls.
But the private companies that the government pays to run the facilities rarely suffer serious financial penalties, even when regulators conclude the companies committed mistakes or paid inadequate attention to safety. Low fines leave taxpayers to finance most of the cleanup and repair of contaminated sites after accidents that officials said never should have happened. ...Los Alamos National Security LLC, was fined $57 million. The government's cleanup bill? Around $1.5 billion.
• Private firms running these laboratories and plants each are paid $40,000 to $160,000 a day in profits alone, a total of more than $2 billion profit in the past 10 years
Nuclear Weapons Site Alarms Shut Off, Scientists Inhale Uranium
Not a clue.
The government scientists didn’t know they were breathing in radioactive uranium at the time it was happening. In fact, most didn’t learn about their exposure for months, long after they returned home from the nuclear weapons research center where they had inhaled it.
The entire event was characterized by sloppiness, according to a quiet federal investigation, with multiple warnings issued and ignored in advance, and new episodes of contamination allowed to occur afterward. All of this transpired without public notice by the center.
Here’s how it happened: ...
(U) Idaho National Laboratory: Cyber Threat and Vulnerability Analysis of the U.S. Electric Sector
(U) DHS Infrastructure Report: Nuclear Reactors, Materials, and Waste Sector Cyberdependencies
... If a single nuclear power reactor goes offline, the electric grid could manage the loss of supply in most (not all) circumstances. Under peak loads, the worst cascading effect might be rolling blackouts until the supply and demand balance.
(U) Potential Terrorist Attack Methods
(U) DHS: National Risk Estimate:Risks to U.S. Critical Infrastructure from Insider Threat
“There are three classes of people: those who see. Those who see when they are shown. Those who do not see.” ― Leonardo da Vinci
Insensible before the wave so soon released by callous fate. Affected most, they understand the least, and understanding, when it comes, invariably arrives too late.
Insensible before the wave so soon released by callous fate. Affected most, they understand the least, and understanding, when it comes, invariably arrives too late.
-

vox_mundi - Intermediate Crude

- Posts: 3939
- Joined: Wed 27 Sep 2006, 03:00:00
Re: Fully Automated Combat Robots Pt. 2
Twilight Zone Was 50 Years Ahead of It's Time
Shape of Thing To Come
For Good Measure ...
To Serve Man - Video
Narration: - These are the players with or without a scorecard- in one corner a machine, and in the other one Wallace V. Whipple, man. And the game, it happens to be the historical battle between flesh and steel, between the brain of man and the product of man's brain. We all may book on this one and predict no winner, but we can tell you for this particular contest, there is standing room only in the Twilight Zone. Video
Plot: In 1967, Wallace V. Whipple, owner of a vast manufacturing corporation, decides to upgrade his plant to increase output by installing a machine named the "X109B14 modified transistorized totally automated machine," which leads to layoffs.
Some former employees try to convince him that the value of a man outweighs the value of a machine, but their protests fall on deaf ears. Eventually, the board of directors find him neurotically obsessed with machines and retire him. Whipple joins his former plant manager (whom Whipple had replaced with a machine) at the bar opposite his factory and expresses deep sorrow at his misfortune ("It isn't fair, Hanley! It isn't fair the way they...diminish us"). A robot now runs his office.
Shape of Thing To Come
Narration: - What you're looking at is a legacy that man left to himself. A decade previous he pushed his buttons and a nightmarish moment later woke up to find that he had set the clock back a thousand years. His engines, his medicines, his science were buried in a mass tomb, covered over by the biggest gravedigger of them all—a bomb. And this is the earth 10 years later, a fragment of what was once a home, a remnant of what was once a race. The year is 1974 and this is The Twilight Zone. Video
Plot: In a sparsely populated town in 1974, ten years after a nuclear war has devastated the US, the townspeople have discovered a supply of canned food. However, they are waiting for Mr. Goldsmith, the town's leader, to return with a message from the mysterious and unseen "old man in the cave" who will tell them whether the food is contaminated with radiation. Some of the townsfolk want to take their chances and eat the food, but they refrain from doing so after seeing the disastrous harvest yielded when they failed to take the old man's advice about which farming areas were contaminated. When Mr. Goldsmith returns, he informs them that the old man has declared the food is contaminated and that it should be destroyed.
Shortly thereafter, a group of soldiers enter the town, led by Major French, and clash with Goldsmith as they try to establish their authority. The soldiers may or may not be representatives of the US government; Goldsmith claims that wandering packs of self-styled military men have previously intruded on the town and tried to establish authority—all unsuccessfully. French, meanwhile, reveals that there are maybe 500 people left alive between Buffalo, New York and Atlanta, Georgia, and also talks of small, isolated primitive societies on the shores of Lake Erie and in "what used to be" Chicago. He claims his job is to organize the region so that society can be re-built. However, Goldsmith believes that French and his men simply want to strip the town of its food.
A clash of wills ensues and, frustrated by Goldsmith's quiet and steadfast refusal to bend, French tries to dispel the townspeople's strange beliefs about the seemingly infallible old man in the cave and take control of the area. French tempts the townspeople with some of the food Goldsmith claimed was contaminated and many throw caution to the wind and partake. Everyone except Goldsmith eventually consumes the food and drink and Goldsmith falls into disfavor among the townspeople. After being bullied and threatened with his life, Goldsmith finally opens the cave door and it is ultimately revealed that in reality, the townsfolk have been listening to a computer the whole time. In a fit of rage at being deceived, the people of the town destroy the computer. However, as Mr. Goldsmith had insisted, the "old man" was correct; without an authority figure to tell them which foods are safe, the entire human population of the town (including the soldiers) die—except for the lone survivor, Mr. Goldsmith.
Mr Goldsmith, survivor. An eyewitness to man's imperfection. An observer of the very human trait of greed. And a chronicler of the last chapter—the one reading "suicide". Not a prediction of what is to be, just a projection of what could be. This has been The Twilight Zone.
For Good Measure ...
To Serve Man - Video
“There are three classes of people: those who see. Those who see when they are shown. Those who do not see.” ― Leonardo da Vinci
Insensible before the wave so soon released by callous fate. Affected most, they understand the least, and understanding, when it comes, invariably arrives too late.
Insensible before the wave so soon released by callous fate. Affected most, they understand the least, and understanding, when it comes, invariably arrives too late.
-

vox_mundi - Intermediate Crude

- Posts: 3939
- Joined: Wed 27 Sep 2006, 03:00:00
Re: Fully Automated Combat Robots Pt. 2
Ukraine Police Say This is the Source of Tuesday’s Massive Cyber Attack
Tuesday’s Massive Ransomware Outbreak Was, In Fact, Something Much Worse
The Petya/GoldenEye Ransomware is Starting to Look Like a Cyberattack in Disguise
Cyberattack Forces West Virginia Hospital to Scrap Computers
Britain prepared to use air strikes or send in troops as retaliation against future cyber attack
(U//FOUO) DHS Critical Infrastructure Note: Healthcare and Public Health Sector Cyberdependencies
The software is called Me.DOC, it’s basically an application for tax reporting and filing for companies that do business in Ukraine. At about 10:30 a.m. GMT Tuesday. MeDoc ran an automatic update on the software, a routine event. That connected every version of Me.Doc on every computer on which it had been installed (so long as it was online) to this address: 92.60.184.55.
That by itself is not unusual.
As the Ukrainian police’s cyber division explained in a Facebook post on Tuesday, updates from Me.doc are usually rather small, about 300 bytes. The update on Tuesday morning ran 333 kilobytes, orders of magnitude larger.
Once host computers download the update — becoming infected — the malware creates a new file called Rundll32.exe. Next it contacts a different network. It then starts running new commands, taking advantage of a particular Windows vulnerability, the same Microsoft vulnerability, called EternalBlue SMB, targeted by Wannacry.
Tuesday’s Massive Ransomware Outbreak Was, In Fact, Something Much Worse
Ukraine Cyberattack Was Meant to Paralyze, not Profit, Evidence Shows
With more time to analyze the malware, researchers on Wednesday are highlighting some curious behavior for a piece of malware that was nearly perfect in almost all other respects: its code is so aggressive that it's impossible for victims to recover their data.
In other words, the researchers said, the payload delivered in Tuesday's outbreak wasn't ransomware at all. Instead, its true objective was to permanently wipe as many hard drives as possible on infected networks, in much the way the Shamoon disk wiper left a wake of destruction in Saudi Arabia. Some researchers have said Shamoon is likely the work of developers sponsored by an as-yet unidentified country. Researchers analyzing Tuesday's malware—alternatively dubbed PetyaWrap, NotPetya, and ExPetr—are speculating the ransom note left behind in Tuesday's attack was, in fact, a hoax intended to capitalize on media interest sparked by last month's massive WCry outbreak."The ransomware was a lure for the media," ... "This version of Petya actually wipes the first sectors of the disk like we have seen with malwares such as Shamoon." He went on to write: "We believe the ransomware was in fact a lure to control the media narrative, especially after the WannaCry incidents, to attract the attention on some mysterious hacker group rather than a national state attacker like we have seen in the past in cases that involved wipers such as Shamoon."
Researchers at antivirus provider Kaspersky Lab, in a blog post published Wednesday, labeled the previous day's malware a "wiper." They explained that for attackers to decrypt a paying victim's computer, they need a "personal infection ID" that's displayed in the ransom note. In the 2016 version of Petya, the ID contained crucial information for the key recovery. Tuesday's malware, by contrast, was generated using pseudorandom data that was unrelated to the corresponding key. Kaspersky Lab researchers Anton Ivanov and Orkhan Mamedov wrote:... Our analysis indicates there is little hope for victims to recover their data. We have analyzed the high-level code of the encryption routine, and we have figured out that, after disk encryption, the threat actor could not decrypt victims' disks. To decrypt a victim's disk, threat actors need the installation ID. In previous versions of "similar" ransomware like Petya/Mischa/GoldenEye, this installation ID contained the information necessary for key recovery. ExPetr does not have that, which means that the threat actor could not extract the necessary information needed for decryption. In short, victims could not recover their data.
The Petya/GoldenEye Ransomware is Starting to Look Like a Cyberattack in Disguise
The haze of yesterday’s massive ransomware attack is clearing, and Ukraine has already emerged as the epicenter of the damage. Kaspersky Labs reports that as many as 60 percent of the systems infected by the Petya ransomware were located within Ukraine, far more than anywhere else. The hack’s reach touched some of the country’s most crucial infrastructure including its central bank, airport, metro transport, and even the Chernobyl power plant, which was forced to move radiation-sensing systems to manual.
The ostensible purpose of all that damage was to make money — and yet there’s very little money to be found. Most ransomware flies under the radar, quietly collecting payouts from companies eager to get their data back and decrypting systems as payments come in. But Petya seems to have been incapable of decrypting infected machines, and its payout method was bizarrely complex, hinging on a single email address that was shut down almost as soon as the malware made headlines. As of this morning, the Bitcoin wallet associated with the attack had received just $10,000, a relatively meager payout by ransomware standards.It leads to an uncomfortable question: what if money wasn’t the point? What if the attackers just wanted to cause damage to Ukraine? It’s not the first time the country has come under cyberattack. (These attacks have typically been attributed to Russia.) But it would be the first time such an attack has come in the guise of ransomware, and has spilled over so heavily onto other countries and corporations.
Because the virus has proven unusually destructive in Ukraine, a number of researchers have come to suspect more sinister motives at work. Peeling apart the program’s decryption failure in a post today, Comae’s Matthieu Suiche concluded a nation state attack was the only plausible explanation:“Pretending to be a ransomware while being in fact a nation state attack, is in our opinion a very subtle way from the attacker to control the narrative of the attack.”
Another prominent infosec figure put it more bluntly: “There’s no fucking way this was criminals.”
There’s already mounting evidence that Petya’s focus on Ukraine was deliberate. The Petya virus is very good at moving within networks, but initial attacks were limited to just a few specific infections, all of which seem to have been targeted at Ukraine. The highest-profile one was a Ukrainian accounting program called MeDoc, which sent out a suspicious software update Tuesday morning that many researchers blame for the initial Petya infections. Attackers also planted malware on the homepage of a prominent Ukraine-based news outlet, according to one researcher at Kaspersky.
In each case, the infections seem to specifically target Ukraine’s most vital institutions, rather than making a broader attempt to find lucrative ransomware targets. These initial infections are particularly telling because they were directly chosen by whoever set the malware in motion. Computer viruses often spread farther than their creators intended, but once Petya was on the loose, the attackers would have had no control over how far it reached. But the attackers had complete control over where they planted Petya initially, and they chose to plant it by some of the most central institutions in Ukraine.Slovakian security software firm ESET released statistics on Thursday showing 75 percent of the infections detected among its global customer base were in Ukraine, and that all of the top 10 countries hit were located in central, eastern or southern Europe.
Arne Schoenbohm, president of BSI, Germany's federal cyber security agency, told Reuters in an interview on Thursday that most of the damage from the attack had hit Ukraine, and Russia to a lesser extent, with only a few dozen German firms affected.
"In all of the known cases, the companies were first infected through a Ukrainian subsidiary," the German official said.
"I think this was directed at us," says Roman Boyarchuk, the head of the Center for Cyber Protection within Ukraine's State Service for Special Communications and Information Protection. "This is definitely not criminal. It is more likely state-sponsored."
As for whether that state sponsor was Russia, "It’s difficult to imagine anyone else would want to do this," Boyarchuk says.
Boyarchuk points to the timing of the attack, just before Ukraine's Constitution Day, which celebrates the country’s post-Soviet independence.“You don’t hit the day before Constitution Day for no reason,” said Craig Williams, the senior technical researcher with the Talos division of Cisco, the American technology company, which helped pinpoint the origin of the Tuesday attack.
Technical experts familiar with the recent history of the cyber escalation between Russia and Ukraine, say these latest attacks are part of the wider political and military conflict, although no "smoking gun" has been found to identify the culprits.
John Hultquist, a cyber intelligence analyst with FireEye, said the failed ransomware attack disguises an as yet unseen destructive motive. "If it were an attack masquerading as crime, that would not be unprecedented at all," Hultquist said.
False Flag: Some cyber security researchers have said the fact that the Kremlin's two flagship energy companies are victims of the attack could suggest Moscow was not behind it.
Russian oil major Rosneft was one of the first companies to reveal it had been compromised by the virus and sources told Reuters on Thursday computers at state gas giant Gazprom had also been infected.
Cyberattack Forces West Virginia Hospital to Scrap Computers
Princeton Community Hospital in rural West Virginia will scrap and replace its entire computer network after being struck by the cyberattack paralyzing computers globally.
The cyberattack, known as Petya, froze the hospital’s electronic medical record system early Tuesday, leaving doctors unable to review patients’ medical history or transmit laboratory and pharmacy orders ...
The U.S. Has Been Attacked - Our Commander-in-Chief's Response ...
Britain prepared to use air strikes or send in troops as retaliation against future cyber attack
(U//FOUO) DHS Critical Infrastructure Note: Healthcare and Public Health Sector Cyberdependencies
(U//FOUO) The Department of Homeland Security (DHS) assesses that given the high value of patient information and proprietary data on the black market, the Healthcare and Public Health Sector will continue to be one of the primary targets for malicious cyber actors. Stolen health data sells on the black market for more than 10 to 20 times the price of stolen credit card data.
(U//FOUO) Electronic Health Records can contain personal data such as names, birth dates, addresses, Social Security numbers, insurance policy numbers, diagnosis codes, billing information, employment information, and income. Criminal and nation-state cyber actors use malware to exfiltrate personally identifiable information (PII), protected health information, and intellectual property data from healthcare companies for illicit financial gain, stock manipulation, or industrial espionage. Malicious cyber actors sell stolen electronic health records on the black market for more than 10 to 20 times the price of stolen credit card data.24,25 Malicious cyber actors can use this data to open new credit accounts, access an individual’s personal financial accounts, falsify medical identities to buy prescription drugs or medical equipment, or file fraudulent claims with insurers.
“There are three classes of people: those who see. Those who see when they are shown. Those who do not see.” ― Leonardo da Vinci
Insensible before the wave so soon released by callous fate. Affected most, they understand the least, and understanding, when it comes, invariably arrives too late.
Insensible before the wave so soon released by callous fate. Affected most, they understand the least, and understanding, when it comes, invariably arrives too late.
-

vox_mundi - Intermediate Crude

- Posts: 3939
- Joined: Wed 27 Sep 2006, 03:00:00
Re: Fully Automated Combat Robots Pt. 2
China Plans to Launch National AI Plan- China Daily
Beijing to set out Artificial Intelligence Development Plan Up to 2030
and in our corner ...
Mnuchin Walks Back AI Statement
China will launch a series of artificial intelligence (AI) projects and increase efforts to cultivate tech talent as part of a soon to announced national AI plan, the China Daily said on Friday, citing a senior official.
The country is focusing on AI as it is seen as a tool to boost productivity and empower employees, the paper said.
China will roll out a slew of AI research and development projects, allocate more resources to nurturing talent and increase the use of AI in education, healthcare and security among other things, said Wan Gang, the minister of science and technology at a conference in Tianjin.
Beijing to set out Artificial Intelligence Development Plan Up to 2030
China’s top technology official said Beijing has laid out a national roadmap to guide the development of artificial intelligence (AI) until the year 2030 as the country’s tech companies pour resources into competing with Western rivals in a race to dominate the field.
It is expected to address issues in four key areas: the building up of AI capability, the application of AI technologies, the introduction of policies to handle the risks brought about by AI – such as job losses – and international collaboration, according to Wan.
His comments were reported by mainland media when he delivered the opening speech of the World Intelligence Congress, China’s first ever official conference on AI, organised by some of the country’s most powerful government organisations, including the top cyber authority.
The soon-to-be-released blueprint is also expected to reveal China’s plans to “rapidly gather AI talent” and “encourage foreign companies to set up research and development centres for AI technologies in China”, he said.
Wan’s speech came amid a rising tide of AI investment and activity in China. Companies large and small all want to get their hands on the technology that forms the basis of myriad real world applications, from facial recognition to more futuristic incarnations like autonomous self-driving vehicles.
All of the country’s top three internet giants, Baidu, Tencent Holding and Alibaba Group have been pushing hard to poach the best AI talent from Silicon Valley, mostly Chinese scientists who study and work in the US.
According to a PwC report released earlier this week, China will see the greatest economic gains globally from AI by 2030, with an estimated 26 per cent boost to its GDP by that time.
and in our corner ...
Mnuchin Walks Back AI Statement
Testifying before the House Ways and Means Committee Wednesday, U.S. Treasury Secretary Steve Mnuchin said he is "fully aware" artificial intelligence will impact jobs, walking back his statement at an Axios event in March that AI won't supplant human jobs for 50-100 more years, which was contrary to most predictions.
Mnuchin Then:"It's not even on our radar screen...50-100 more years" away. "I'm not worried at all" about robots displacing humans in the near future.
Mnuchin Now: "When I made the comment on artificial intelligence — and there's different views on artificial intelligence — I was referring to kind of like R2D2 in Star Wars. Robotics are here. Self-driving cars are something that are gonna be here soon. I am fully aware of and agree that technology is changing and our workers do need to be prepared."
Separated at Birth?
“There are three classes of people: those who see. Those who see when they are shown. Those who do not see.” ― Leonardo da Vinci
Insensible before the wave so soon released by callous fate. Affected most, they understand the least, and understanding, when it comes, invariably arrives too late.
Insensible before the wave so soon released by callous fate. Affected most, they understand the least, and understanding, when it comes, invariably arrives too late.
-

vox_mundi - Intermediate Crude

- Posts: 3939
- Joined: Wed 27 Sep 2006, 03:00:00
Re: Fully Automated Combat Robots Pt. 2
The Immaculate Infection
Maersk says global IT breakdown caused by cyber attack
Global Shipping Feels Fallout from Maersk Cyber Attack
Companies Still Hobbled by Fearsome Cyber Attack
Global cyber attack likely cover for malware installation in Ukraine: police official
Ukraine points finger at Russian security services in recent cyber attack
Law Firm DLA Piper Reels Under Cyber Attack, Fate of Files Unclear
HMS Windows XP: Britain's newest warship running Swiss Cheese OS
Michael Flynn Worked With Foreign Cyberweapons Group That Sold Spyware Used Against Political Dissidents
Spy Agencies Seek Permanent Authority for Contested Surveillance Program
NSA Surveillance Techniques: How Your Data Becomes Our Data
Google will stop scanning your Gmail messages to sell targeted ads
... Rosneft, a Russian state controlled company (that does not use MeDoc), was also hit by the worm. They managed to escape practically unscathed, evading all the lateral traversal mechanisms of the worm and simply switching to their backup system. Fortunately, all this without even an interruption to their operations.
Although there has been talk that the Russian oil sector was also hit, their infinitely superior cybersecurity skills meant that they suffered no downtime or outages. Curious that they were so poorly protected they got infected — especially since they aren’t connected to MeDoc (the initial infection vector) — however they were so well protected they were able to remediate the infection (which didn’t spread… although it can take out 5000 computers in less than 10 minutes.)
Once is an accident. Twice is a coincidence. Three times is an enemy action.
— Goldfinger, by Ian Fleming
... This was a straight forward cyber attack with a target space of basically every company that does business in UkraineSeriously, that blast radius is ‘taxable presence in Ukraine.’ I don’t like reading tea leaves, but that isn’t exactly subtle.
https://twitter.com/marasawr/status/879 ... afd1ee89d4
... Robert M. Lee, CEO of Dragos Inc. and an expert on cyberattacks on infrastructure including Ukraine's power grid, said:... the rules of cyberespionage appear to be changing, with sophisticated actors—state-sponsored or not—violating what had been established norms of avoiding collateral damage.
Maersk says global IT breakdown caused by cyber attack
Shipping giant A.P. Moller-Maersk (MAERSKb.CO), which handles one out of seven containers shipped globally, said the Petya cyber attack had caused outages at its computer systems across the world on Tuesday.
Global Shipping Feels Fallout from Maersk Cyber Attack
Containers are piled up at a terminal at the Jawaharlal Nehru Port Trust in Mumbai, India, Thursday, June 29, 2017. Operations at a terminal at India's busiest container port have been stalled by the malicious software
The cyber attack was among the biggest-ever disruptions to hit global shipping. Several port terminals run by a Maersk division, including in the United States, India, Spain, the Netherlands, were still struggling to revert to normal operations on Thursday after experiencing massive disruptions.
South Florida Container Terminal, for example, said dry cargo could not be delivered and no container would be received. Anil Diggikar, chairman of JNPT port, near the Indian commercial hub of Mumbai, told Reuters that he did not know "when exactly the terminal will be running smoothly".
His uncertainty was echoed by Maersk itself, which told Reuters that a number of IT systems were still shut down and that it could not say when normal business operations would be resumed."As Maersk is about 18 percent of all container trade, can you imagine the panic this must be causing in the logistic chain of all those cargo owners all over the world?" ... "Right now none of them know where any of their cargoes (or)containers are. And this 'black hole' of lack of knowledge will continue till Maersk are able to bring back their systems on line."
- Khalid Hashim, managing director of Precious Shipping (PSL.BK), Thailand's largest dry cargo ship owners
About 90 percent of world trade is transported by sea, with ships and ports acting as the arteries of the global economy. Ports increasingly rely on communications systems to keep operations running smoothly, and any IT glitches can create major disruptions for complex logistic supply chains.
The impact of the attack on the company has reverberated across the industry given its position as the world's biggest container shipping line and also operator of 76 ports via its APM Terminals division.
Container ships transport much of the world's consumer goods and food, while dry bulk ships haul commodities including coal and grain and tankers carry vital oil and gas supplies.
Companies Still Hobbled by Fearsome Cyber Attack
Many businesses still struggled Friday to recover hopelessly scrambled computer networks, collateral damage from a massive cyberattack that targeted Ukraine three days ago.
The Heritage Valley Health System couldn't offer lab and diagnostic imaging services at 14 community and neighborhood offices in western Pennsylvania. DLA Piper, a London-based law firm with offices in 40 countries, said on its website that email systems were down; a receptionist said email hadn't been restored by the close of business day.
Dave Kennedy, a former Marine cyberwarrior who is now CEO of the security company TrustedSec, said one U.S. company he is helping is rebuilding its entire network of more than 5,000 computers. Kennedy added:
"Some of these companies are actually using pieces of paper to write down credit card numbers. It's crazy."
"It hit everything, their backups, servers, their workstations, everything," he said. "Everything was just nuked and wiped."
Microsoft said NotPetya hit companies in at least 64 nations, including Russia, Germany and the United States. Victims include drug giant Merck & Co. and the shipping company FedEx's TNT subsidiary. Trade in FedEx stock was temporarily halted Wednesday
One major victim, Danish shipping giant A.P. Maersk-Moller, said Friday that its cargo terminals and port operations were "now running close to normal again." It said operations had been restored in Spain, Morocco, India, Brazil, Argentina and Lima, Peru, but problems lingered in Rotterdam, the Netherlands; Elizabeth, New Jersey; and Los Angeles.
An employee at an international transit company at Lima's port of Callao told The Associated Press that Maersk employees' telephone system and email had been knocked out by the virus—so they were "stuck using their personal cellphones." The employee spoke on condition of anonymity because he's not authorized to speak to reporters.
Global cyber attack likely cover for malware installation in Ukraine: police official
... A growing consensus among security researchers, armed with technical evidence, suggests the main purpose of the attack was to install new malware on computers at government and commercial organizations in Ukraine. Rather than extortion, the goal may be to plant the seeds of future sabotage, experts said.
... "It's highly likely that during this attack new attacks were set up," said ISSP chairman Oleg Derevianko.
"At almost all organizations whose network domains were infected, not all computers went offline," he said by phone. "Why didn't they all go offline? We are trying to understand what they might have left on those machines that weren't hit."
... NotPetya does not randomly scan the Internet to find new computers to infect. It only spreads itself inside organizational networks, taking advantage of a variety of legitimate network administration tools.
This makes it far harder for anti-virus software or network security technicians to detect. It also gives it the capacity to infect other Windows computers, even those with the latest security patches, several security firms warned on Thursday.
"Petya is proving to be more sophisticated than WannaCry in terms of scope, ability to be neutralized, and apparently, the motivation behind its launch," corporate security consulting firm Kroll has advised its clients.
Ukraine points finger at Russian security services in recent cyber attack
The SBU, Ukraine's state security service, said the attack, which started in Ukraine and spread around the world on Tuesday, was by the same hackers who attacked the Ukrainian power grid in December 2016.
... "The available data, including those obtained in cooperation with international antivirus companies, give us reason to believe that the same hacking groups are involved in the attacks, which in December 2016 attacked the financial system, transport and energy facilities of Ukraine using TeleBots and BlackEnergy," the SBU, said.
Law Firm DLA Piper Reels Under Cyber Attack, Fate of Files Unclear
A prominent global law firm, which has touted its expertise on cybersecurity, is still struggling to recover from vicious computer attacks unleashed on Tuesday by hackers.
As of Thursday, it appears DLA Piper has yet to fully resume basic operations, including email, or to publicly confirm whether the firm's documents or those of its clients were destroyed in the attack.
HMS Windows XP: Britain's newest warship running Swiss Cheese OS
The Royal Navy’s brand new £3.5bn aircraft carrier HMS Queen Elizabeth is currently* running Windows XP in her flying control room, according to reports.
Defence correspondents from The Times and The Guardian, when being given a tour of the carrier’s aft island – the rear of the two towers protruding above the ship’s main deck – spotted Windows XP apparently in the process of booting up on one of the screens in the flying control room, or Flyco.
“A computer screen inside a control room on HMS Queen Elizabeth was displaying Microsoft Windows XP – copyright 1985 to 2001 – when a group of journalists was given a tour of the £3 billion warship last week,” reported Deborah Haynes of The Times, accurately describing the copyright information on the XP loading screen.
Similarly, the Guardian’s Ewen MacAskill (who also worked on the Edward Snowden NSA revelations in 2013) noted: “During a tour of the carrier, screens were spotted using what appeared to be the outdated 2001 Windows XP operating system.”
Michael Flynn Worked With Foreign Cyberweapons Group That Sold Spyware Used Against Political Dissidents
Spy Agencies Seek Permanent Authority for Contested Surveillance Program
NSA Surveillance Techniques: How Your Data Becomes Our Data

In 2001, NSA published the secret "Transition 2001" report defining our strategy for the 21st century. No longer could we simply access analog communications using conventional means, the new digital world of globally-networked encrypted communications required a dramatic change to our surveillance strategy: NSA would need to "live on the network".
We've turned our nation's Internet and telecommunications companies into collection partners by installing filters in their facilities, serving them with secret court orders, building back doors into their software and acquiring keys to break their encryption.
NSA technicians have installed intercept stations at key junction points, or switches, throughout the country. These switches are located in large windowless buildings owned by the major telecommunication companies and control the domestic internet traffic flow across the nation. A fiber optic splitter is placed on the incoming communication lines and routes the traffic to an NSA intercept station for processing.
View a sample route that internet data traverses from a home in Toronto to the San Francisco Art Institute passing through several NSA intercept stations.
Google will stop scanning your Gmail messages to sell targeted ads
“There are three classes of people: those who see. Those who see when they are shown. Those who do not see.” ― Leonardo da Vinci
Insensible before the wave so soon released by callous fate. Affected most, they understand the least, and understanding, when it comes, invariably arrives too late.
Insensible before the wave so soon released by callous fate. Affected most, they understand the least, and understanding, when it comes, invariably arrives too late.
-

vox_mundi - Intermediate Crude

- Posts: 3939
- Joined: Wed 27 Sep 2006, 03:00:00
Re: Fully Automated Combat Robots Pt. 2
Scientists Harness 'Mind Reading' Technology to Decode Complex Thoughts
Previously ...
Mind-Reading Tech Reconstructs Videos From Brain Images
http://www.ccbi.cmu.edu/reprints/Wang_J ... eprint.pdf
Carnegie Mellon University scientists can now use brain activation patterns to identify complex thoughts, such as, "The witness shouted during the trial."
This latest research led by CMU's Marcel Just builds on the pioneering use of machine learning algorithms with brain imaging technology to "mind read." The findings indicate that the mind's building blocks for constructing complex thoughts are formed by the brain's various sub-systems and are not word-based. Published in Human Brain Mapping and funded by the Intelligence Advanced Research Projects Activity (IARPA), the study offers new evidence that the neural dimensions of concept representation are universal across people and languages.
"One of the big advances of the human brain was the ability to combine individual concepts into complex thoughts, to think not just of 'bananas,' but 'I like to eat bananas in evening with my friends,'" said Just, the D.O. Hebb University Professor of Psychology in the Dietrich College of Humanities and Social Sciences."We have finally developed a way to see thoughts of that complexity in the fMRI signal. The discovery of this correspondence between thoughts and brain activation patterns tells us what the thoughts are built of."
The new study demonstrates that the brain's coding of 240 complex events, sentences like the shouting during the trial scenario uses an alphabet of 42 meaning components, or neurally plausible semantic features, consisting of features, like person, setting, size, social interaction and physical action. Each type of information is processed in a different brain system—which is how the brain also processes the information for objects. By measuring the activation in each brain system, the program can tell what types of thoughts are being contemplated.
For seven adult participants, the researchers used a computational model to assess how the brain activation patterns for 239 sentences corresponded to the neurally plausible semantic features that characterized each sentence. Then the program was able to decode the features of the 240th left-out sentence. They went through leaving out each of the 240 sentences in turn, in what is called cross-validation.
The model was able to predict the features of the left-out sentence, with 87 percent accuracy, despite never being exposed to its activation before. It was also able to work in the other direction, to predict the activation pattern of a previously unseen sentence, knowing only its semantic features.
He added, "A next step might be to decode the general type of topic a person is thinking about, such as geology or skateboarding. We are on the way to making a map of all the types of knowledge in the brain."
Previously ...
Mind-Reading Tech Reconstructs Videos From Brain Images
Video - It sounds like science fiction: while volunteers watched movie clips, a scanner watched their brains. And from their brain activity, a computer made rough reconstructions of what they viewed.
Scientists reported that result Thursday in the US and speculated such an approach might be able to reveal dreams and hallucinations someday.
The new work was published online on Thursday by the journal Current Biology. It's a step beyond previous work that produced similar results with still images.
http://gallantlab.org/index.php/publica ... t-al-2011/
http://journal.frontiersin.org/article/ ... 00081/full
“There are three classes of people: those who see. Those who see when they are shown. Those who do not see.” ― Leonardo da Vinci
Insensible before the wave so soon released by callous fate. Affected most, they understand the least, and understanding, when it comes, invariably arrives too late.
Insensible before the wave so soon released by callous fate. Affected most, they understand the least, and understanding, when it comes, invariably arrives too late.
-

vox_mundi - Intermediate Crude

- Posts: 3939
- Joined: Wed 27 Sep 2006, 03:00:00
Re: Fully Automated Combat Robots Pt. 2
...U.S. Treasury Secretary Steve Mnuchin Now:"When I made the comment on artificial intelligence — I was referring to kind of like R2D2 in Star Wars. ..."
We Got Your R2D2 Right Here Pal ...
SU Robotics Program Builds Functioning R2-D2 Robots
POCATELLO — What started as a senior project for a student enrolled in Idaho State University’s College of Technology Robotics program has evolved into something that many Star Wars fans have dreamed of for decades — designing and building a fully-functional R2-D2 robot.
The Robotics program has one fully constructed R2-D2 robot and another that’s under construction that program director Shane Slack said is hopeful will be done in time for September’s Snake River Comic Con in Pocatello.
DARPA Teaches Robots 'Manners, Etiquette and Protocol' like C-3PO — Translation's Already Covered
Video - Advances in artificial intelligence (AI) are making virtual and robotic assistants increasingly capable in performing complex tasks. For these “smart” machines to be considered safe and trustworthy collaborators with human partners, however, robots must be able to quickly assess a given situation and apply human social norms. Such norms are intuitively obvious to most people—for example, the result of growing up in a society where subtle or not-so-subtle cues are provided from childhood about how to appropriately behave in a group setting or respond to interpersonal situations. But teaching those rules to robots is a novel challenge.Avoid AI fails like: ‘Glad to hear your family died!’
To address that challenge, DARPA-funded researchers recently completed a project that aimed to provide a theoretical and formal framework for what norms and normative networks are; study experimentally how norms are represented and activated in the human mind; and examine how norms can be learned and might emerge from novel interactive algorithms. The team was able to create a cognitive-computational model of human norms in a representation that can be coded into machines, and developed a machine-learning algorithm that allows machines to learn norms in unfamiliar situations drawing on human data.
The work represents important progress towards the development of AI systems that can “intuit” how to behave in certain situations in much the way people do.As an example in which humans intuitively apply social norms of behavior, consider a situation in which a cell phone rings in a quiet library. A person receiving that call would quickly try to silence the distracting phone, and whisper into the phone before going outside to continue the call in a normal voice. Today, an AI phone-answering system would not automatically respond with that kind of social sensitivity.
Ultimately, for a robot to become social or perhaps even ethical, it will need to have a capacity to learn, represent, activate, and apply a large number of norms that people in a given society expect one another to obey, Ghanadan said. That task will prove far more complicated than teaching AI systems rules for simpler tasks such as tagging pictures, detecting spam, or guiding people through their tax returns. But by providing a framework for developing and testing such complex algorithms, the new research could accelerate the day when machines emulate the best of human behavior.
Battery-Free Self Driving Potato (Uncooked)
Many, many potatoes were almost certainly harmed in the making of this video.
Last edited by vox_mundi on Mon 03 Jul 2017, 13:21:09, edited 1 time in total.
“There are three classes of people: those who see. Those who see when they are shown. Those who do not see.” ― Leonardo da Vinci
Insensible before the wave so soon released by callous fate. Affected most, they understand the least, and understanding, when it comes, invariably arrives too late.
Insensible before the wave so soon released by callous fate. Affected most, they understand the least, and understanding, when it comes, invariably arrives too late.
-

vox_mundi - Intermediate Crude

- Posts: 3939
- Joined: Wed 27 Sep 2006, 03:00:00
Return to Geopolitics & Global Economics
Who is online
Users browsing this forum: No registered users and 7 guests





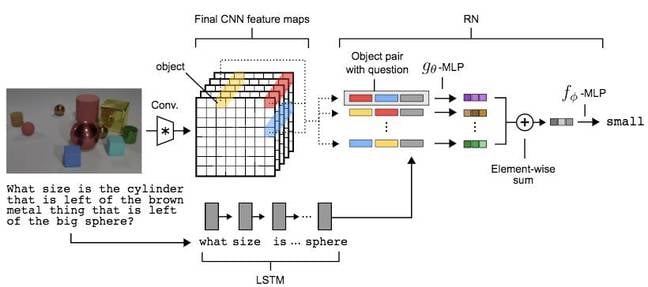

























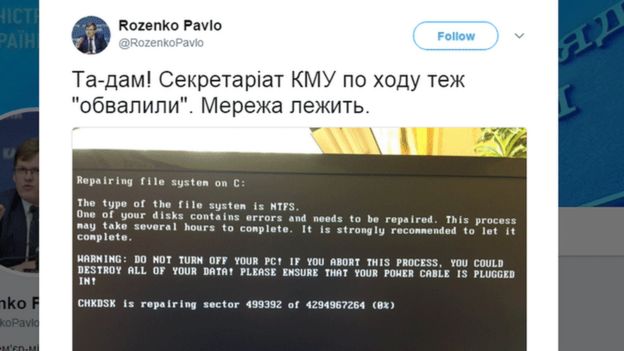






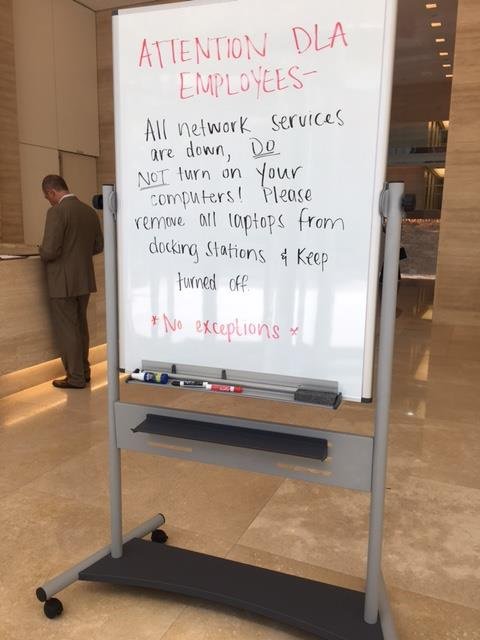



:origin()/pre15/5f44/th/pre/f/2010/334/0/6/capitalism_demotivator_by_party9999999-d33x22t.jpg)