In a presentation at the Black Hat conference in Las Vegas on Wednesday, Billy Rios, founder of security shop Whitescope, and Jonathan Butts, committee chair for the IFIP Working Group on Critical Infrastructure Protection, showed how easy it was to compromise a widely used car wash system: the Laserwash series manufactured by PDQ, based in Wisconsin, USA.
The hardware's control system is an embedded WindowsCE computer powered by an ARM-compatible processor. However, Microsoft no longer supports the version of WinCE used in the kit, Rios said, meaning it may be possible to commandeer the machinery by exploiting security vulnerabilities lingering in the operating system.However, there was no need to find and exploit old WinCE holes to remotely break into one of these bad boys. Once the infosec duo had found a suitable car wash connected to the web, the researchers found that the default password – 12345 – just worked. Once logged in from their browser, they were given full control of the system.
From there, they could prod the web app into doing things it really shouldn't.
Like this ...and This
“Car washes are really just industrial control systems. The attitudes of ICS are still in there,” Rios said. “We’ve written an exploit to cause a car wash system to physically attack; it will strike anyone in the car wash. We think this is the first exploit that causes a connected device to attack someone.”
In their talk the pair showed how they managed to bypass the safety sensors on the car wash doors to close them on a car entering the washer. Butts told The Register that much more destructive hacks were possible.“We controlled all the machinery inside the car wash and could shut down the safety systems,” he said. “You could set the roller arms to come down much lower and crush the top of the car, provided there was not mechanical barriers in place.”
That's another reason to support your local bikini car wash
Flaws in Web-connected, Radiation-Monitoring Kit? What Could Go Wrong?
Black Hat Vulnerabilities in widely deployed Radiation Monitoring Devices (RDMs) present a potential mechanism for triggering false alarms and worse, according to research unveiled at Black Hat on Wednesday.
An inspection of the technology by Ruben Santamarta, principal security consultant for IOActive, uncovered flaws in RDMs from multiple vendors, including Ludlum and Mirion. Santamarta's research focused on testing software and hardware, firmware reverse engineering and radio frequency analysis.
The vulnerabilities create a means to meddle with "critical systems used for monitoring radiation levels, for example by falsifying measurement readings to simulate a radiation leak, tricking authorities to give incorrect evacuation directions, or increasing the time an attack against a nuclear facility or an attack involving a radioactive material remains undetected by sending normal readings to deceive operators"."Being able to properly and accurately detect radiation levels is imperative in preventing harm to those at or near nuclear plants and other critical facilities, as well as for ensuring radioactive materials are not smuggled across borders."
Inspection of software that ships with the Model 53 Gamma Personnel Portal from Ludlum revealed a backdoor password. "As a result, malicious personnel can bypass the RPM's authentication and take control of the device, which could be used to disable it, thus preventing the RPM from triggering proper alarms," Santamarta warned.
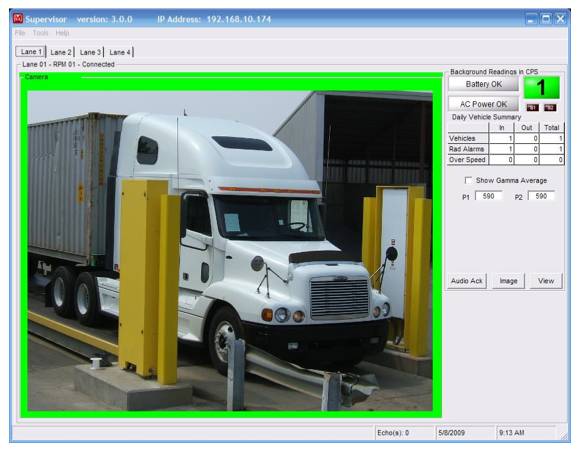
Ludlum's gate monitors – Model 4525 – for vehicle inspection lack any security measure for data communication. Any attacker in the adjacent network can change the device's network settings, which opens the door to multiple attacks. Worse yet, the device communicates via cleartext, so attackers would be able to falsify readings, disable alarms, or perform any other originally supported operation.
Ludlum's gate monitors – Model 4525 – for vehicle inspection (at Ports, Border Crossing, Nuclear Power Plants)
Cyber Attacks on Critical Infrastructure: Insights from War Gaming
The Department of Homeland Security’s Industrial Control Systems Cyber Emergency Response Team says it has never seen so many successful exploitation attempts on the control system layer of industrial systems. That means hackers are increasingly infiltrating the networks of major industrial operations all the way down to the sensors and systems that manage our digitized worlds. Major U.S. infrastructures — electric grids, dams, wastewater, and critical manufacturing — are vulnerable to physical damage from cyber attack.This has created a unique national security problem for the United States. For the first time in modern American history, a prolific set of adversaries can target the homeland with little warning and at low cost. This creates a soft-underbelly target for state and non-state actors motivated by greed, opportunism, radical beliefs, or good old-fashioned state coercion.
... Our wargame suggested that the most dangerous cyber attacks were those that caused cascading effects across sectors. Cross-sector dependencies on electricity, transportation, and wastewater systems made significant attacks on these sectors exponentially more deleterious than attacks on stand-alone sectors such as commercial facilities or the defense industrial base. Unfortunately, the complex interdependence of sectors makes these attacks not only the most likely to create catastrophic consequences, but also the least conducive to current information-sharing and crisis management techniques.
TNT Cyber-attack Crippling Small Firms, Says FSB
Small firms are being "crippled" by the continuing impact of last month's NotPetya cyber attack on Dutch delivery firm TNT, a business group has warned.
The Federation of Small Businesses (FSB) says it has "serious concerns" over the effects of the 28 June attack."[It] has been debilitating for some small firms who remain in the dark over when, and if, they can expect their goods to be delivered"
"This is a stark reminder of the danger posed by cyber-crime and how it can strike down smaller businesses indirectly, having a much wider impact on the economy.
Frustrated customers trying to get news of their undelivered parcels have been told by TNT’s UK staff that consignments at its East Midlands hub are “going up to the ceiling” as international shipments are still having to be processed by hand.
U.S. Treads Water on Cyber Policy as Destructive Attacks Mount
SAN FRANCISCO (Reuters) - The Trump administration's refusal to publicly accuse Russia and others in a wave of politically motivated hacking attacks is creating a policy vacuum that security experts fear will encourage more cyber warfare.
... "I see no dynamics of deterrence," said ex-White House cyber security officer Jason Healey, now at Columbia University.
The government retreat is underscored by the departure at the end of July of Chris Painter, the official responsible for coordinating U.S. diplomacy on cyber security. No replacement has been named and the future of the position in the State Department is in flux.
The policy vacuum left by the United States is also affecting private security firms, which say they have grown more cautious in publicly attributing cyber attacks to nation-states lest they draw fire from the Trump administration.
Trump suggested in an April interview that the security firm CrowdStrike, which worked on investigating the election hack of the Democratic National Committee, might not be trustworthy because he was told it was controlled by a Ukrainian. It is not.
U.S. Defense Budget May Help Fund "Hacking for Defense" Classes at Universities
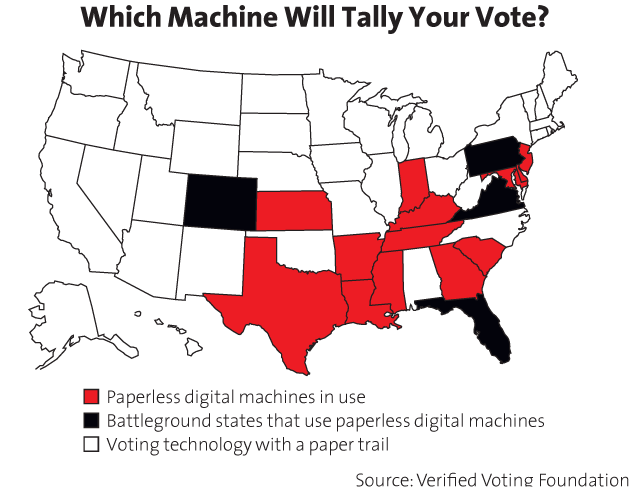
Hacking the Vote: Who Helped Whom?
In recent months, we have learned much about how successful the Trump campaign was in micro-targeting voters in crucial swing states. In the waning days of the 2016 campaign, especially, Trump’s data team knew exactly which voters in which states they needed to persuade on Facebook and Twitter and precisely what messages to use. The question is: How did the Russians know this, too?
Computer models get stronger, and more robust, the more information they have. It is likely that no one knows this better than the major Trump donor Robert Mercer, who was a central architect of IBM’s Watson artificial intelligence engine before he became a hedge fund billionaire, Breitbart investor, and primary owner of Cambridge Analytica.
Last week, it was reported that both Congressional investigators and the FBI are now exploring whether Russian operatives were guided in their efforts by Trump’s digital team, and the House Intelligence Committee has invited Trump’s digital director, Brad Parscale, to testify. Largely ignored in this discussion, however, is another possibility: that the Russians themselves, through their hacking of Democratic Party records, were supplying crucial information to the digital team.
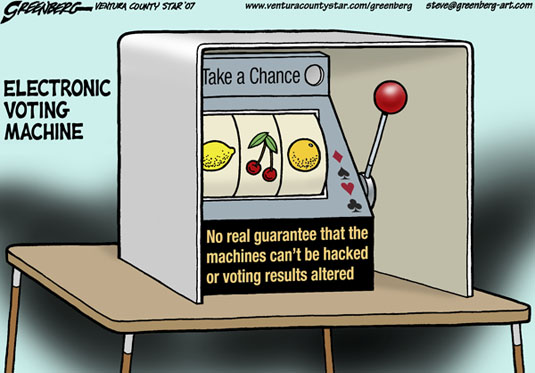
Hackers Plan To Break into 30 Voting Machines To Put Election Meddling to the Test
Just how secure is the U.S. election systems? Hackers aim to find out.
LAS VEGAS – Think of it as a stress test for democracy. Hackers plan to spend this weekend trying to break into more than 30 voting machines used in recent elections to see just how far they can get.
U.S. election officials have consistently said that despite Russian attempts to affect the outcome of the 2016 presidential election, no votes were tampered with.
Prove it, say organizers of DefCon, an annual hacker convention held in Las Vegas each July.
The idea is to “start hacking on (the machines) to raise awareness and find out for ourselves what the deal is. I'm tired of reading misinformation about voting system security,” Jeff Moss, DefCon founder, wrote on the conference blog.
This will be the first time a technical crowd will have the ability to look at the machines “on a large scale.” That’s in part because until 2015, it was illegal under the terms of the Digital Millennium Copyright Act to try to hack into voting machines.
Experts in election voting software say no states routinely perform post-election vote audits to ensure that the reported vote count tallies with ballots, Singer said.
Moreover, there were no forensic examinations of any of the voting machines used in the 2016 presidential election, in part because many election-machine vendor contracts prohibit it, Singer said.
That’s a red flag for hackers at DefCon.
... The effort is being overseen by two well-known researchers in the field of election security, Blaze and Harri Hursti, a Finnish computer programer who in 2005 showed it was possible to hack into a Diebold voting machine and change vote tallies, a technique now known as “the Hursti Hack.”
“Election machines used in USA really do not have security standards - the voluntary voting system standard addresses air humidity and shock resistance, but not security. This means that the old systems which were designed with no security consciousness are not being replaced with responsibly designed successors,” said Harri Hursti, a Finnish computer programmer who has worked on election-related issues in Finland, the United Kingdom, Estonia, Argentina and the United States. “Also, vendors are frequently blatantly mispresenting the specifications and the properties of the equipment they sell to the jurisdictions.”
Watch This Security Researcher Hack a Voting Machine
If Voting Machines Were Hacked, Would Anyone Know?









































































 ...
...